Most security incidents do not begin with a dramatic breakthrough. They begin with a gap that already exists: an exposed admin panel, a forgotten server, a cloud setting that grants too much access, a dependency nobody realized was in production, or a routine approval that can be socially engineered.
A vulnerability is that gap. It is any weakness in technology, configuration, process, or human behavior that can be used to compromise confidentiality, integrity, or availability.
This article explains what a vulnerability is, how it differs from related concepts, the forms it takes in modern environments, and how to manage vulnerabilities in a way that reduces real-world risk instead of generating endless backlogs.
What a Vulnerability Is in Cybersecurity
A vulnerability is a weakness that creates an opportunity for an attacker. It can live in software, hardware, identity systems, cloud configurations, operational processes, and everyday workflows.
A useful way to keep terms clean is to separate weakness, likelihood, and method:
- Vulnerability: the weakness that makes compromise possible
- Threat and risk: the likelihood and impact if the weakness is targeted
- Exploit: the technique or code path used to take advantage of the weakness
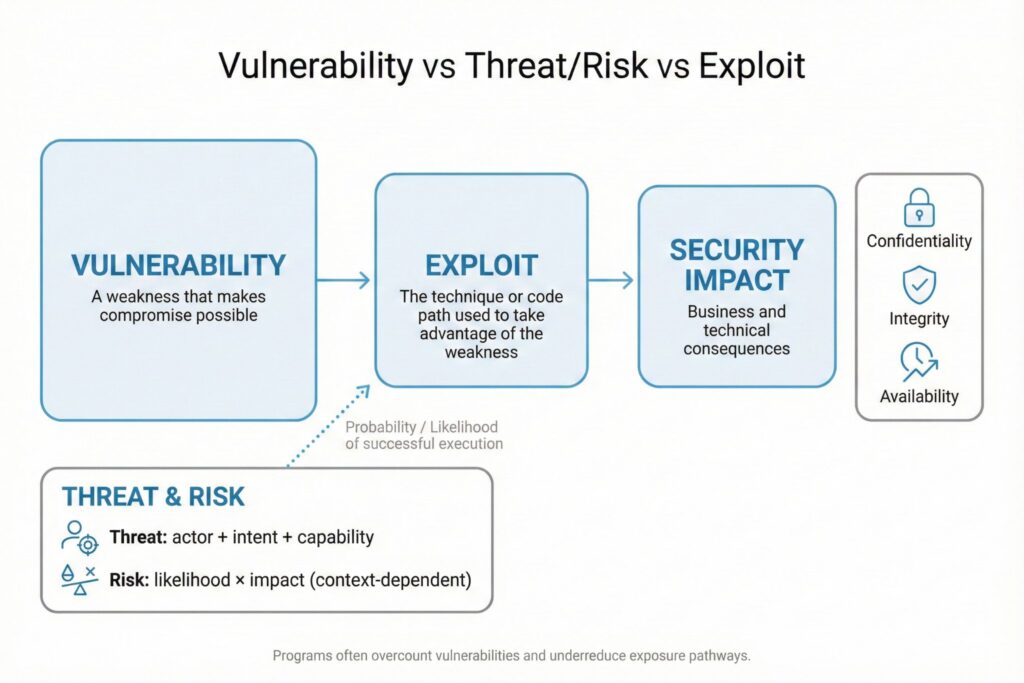
This distinction matters because many programs overinvest in cataloging vulnerabilities and underinvest in reducing exposure pathways that make exploitation likely.
Why Vulnerabilities Exist Even in Mature Environments
Even strong organizations accumulate vulnerabilities for structural reasons:
First, environments change faster than governance. New SaaS tools, new cloud resources, and new integrations arrive weekly, while inventory and policy updates lag behind.
Second, ownership is distributed. Security may see the risk, but engineering owns the code, IT owns the endpoints, and product teams own the deadlines. Vulnerabilities often sit in the gaps between responsibilities.
Third, complexity creates silent failure modes. A control can be deployed but ineffective due to misconfiguration, missing coverage, or inconsistent enforcement.
Finally, attackers only need one reliable path. Defenders must manage thousands of moving parts, and a single weak spot can create a chain reaction.
The Most Common Vulnerability Types Today
Modern breaches frequently involve combinations: a technical weakness plus weak identity controls plus a workflow mistake. The most common categories include:
- Unpatched software and unsupported systems: known issues remain open because updates are delayed or platforms are end of life
- Misconfiguration and overexposure: public storage, overly permissive firewall rules, exposed remote management, excessive cloud IAM permissions
- Authentication and authorization gaps: missing MFA on privileged access, weak recovery flows, session token leakage, broken access checks in applications
- Insecure dependencies and supply chain drift: vulnerable libraries embedded in builds, containers, and third-party components
- Human and process weaknesses: phishing susceptibility, approval processes that rely on email alone, weak separation of duties
These categories overlap. For example, a cloud misconfiguration often becomes critical only when paired with broad identity permissions and weak logging.
Vulnerabilities, Zero Days, and Known Issues
A vulnerability can be known or unknown.
Known vulnerabilities are tracked through public identifiers and repositories, commonly via CVE entries. Unknown vulnerabilities include zero days, which are weaknesses not yet publicly disclosed or not yet fixed by a vendor.
Both matter, but they require different strategies:
Known vulnerabilities are managed through inventory, prioritization, patching, configuration hardening, and compensating controls.
Zero days are managed through resilience: least privilege, segmentation, strong identity, rapid detection, and the ability to contain impact when an unexpected weakness is exploited.
A Real Example: Log4Shell
Log4Shell, tracked as CVE-2021-44228, is widely cited because it shows how a single component can create widespread exposure across organizations. The National Vulnerability Database description explains how certain Log4j2 versions could allow remote code execution when attacker-controlled lookups are processed, and it details the impacted versions and mitigation behavior changes in later releases.
The lesson is broader than one CVE: if you cannot quickly answer where a component runs, who owns it, and how it is exposed, remediation speed collapses when the next high-impact issue appears.
Why Vulnerabilities Matter to the Business
Vulnerabilities are not an abstract technical problem. They convert into downtime, fraud, data loss, regulatory exposure, incident response costs, and reputational damage.
IBM’s Cost of a Data Breach Report 2025 reports a global average cost of a data breach of USD 4.44 million, down from USD 4.88 million in 2024.
That number is an average, not a forecast for every organization, but it clarifies the scale: vulnerabilities that remain exploitable can become business events.
What Vulnerability Management Should Accomplish
A vulnerability management program is effective only if it produces measurable risk reduction. Counting vulnerabilities, generating dashboards, and closing tickets are not outcomes. Outcomes are fewer exploitable paths to critical assets and faster containment when compromise happens.
The most practical definition is: continuous identification, prioritization, and remediation of weaknesses, aligned to business impact and attacker behavior.
NIST guidance on patch management frames patching as preventive maintenance and emphasizes planning as a core enterprise capability rather than an ad hoc reaction to alerts.
How to Prioritize Vulnerabilities Without Drowning
Severity scoring helps, but it does not solve prioritization by itself.
CVSS is widely used as a severity framework and is maintained by FIRST, with current resources for CVSS v4.0 available through FIRST.
To prioritize what to fix first, combine severity with signals of real-world exploitation and local business context.
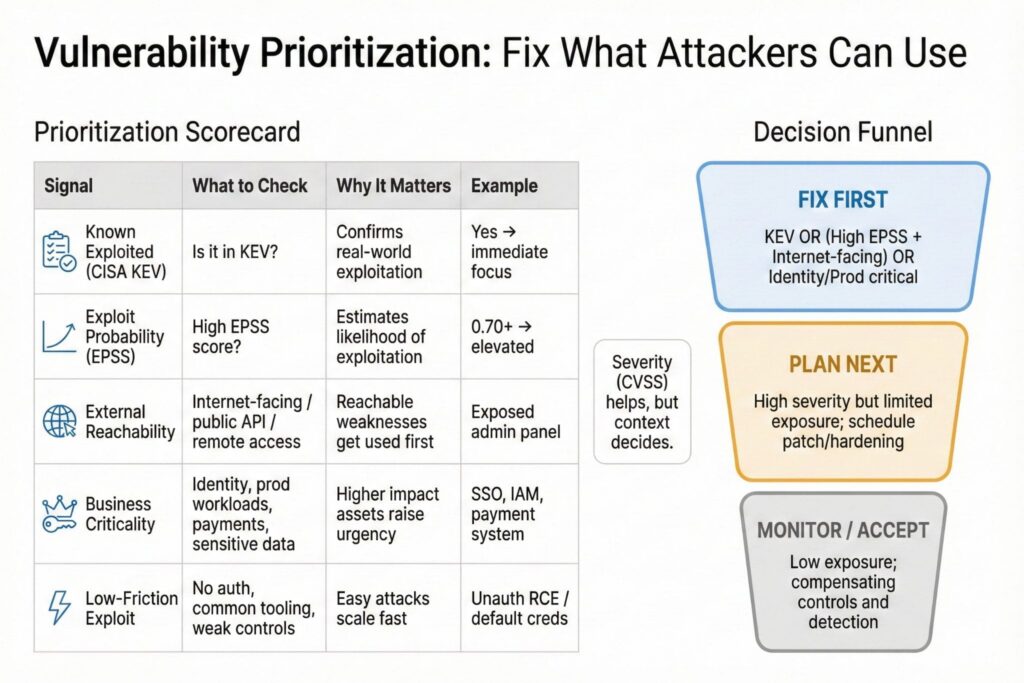
Two widely used signals are:
- CISA maintains the Known Exploited Vulnerabilities Catalog as an authoritative list of vulnerabilities exploited in the wild.
- FIRST EPSS provides a probability score estimating the likelihood a vulnerability will be exploited, expressed as a value between 0 and 1.
A practical prioritization checklist that works in most environments:
- Is it known to be exploited: check CISA KEV for confirmed exploitation
- Is it externally reachable or widely exposed: internet-facing services, remote access gateways, public APIs, partner connectivity
- Does it touch high-impact assets: identity systems, production workloads, payment flows, sensitive data, core business platforms
- Is exploitation low friction: no authentication required, common exploit tooling available, weak compensating controls
- Is there a fast mitigation: patch, configuration change, feature disablement, access restriction, segmentation, or detection rule
This approach reduces panic patching and helps teams focus on what attackers can actually use to reach valuable targets.
Remediation Options That Reduce Risk Fast
Fixing a vulnerability does not always mean applying a patch immediately. The correct remediation depends on operational constraints and exposure.
Common remediation paths include:
- Patching or upgrading to remove the weakness
- Reconfiguring to close unnecessary exposure
- Reducing privileges and tightening identity controls
- Segmentation and access controls that reduce reachability
- Compensating monitoring and detection until a full fix is available
- Removing unused services, unused accounts, and unused dependencies
The most overlooked remediation is removing what nobody uses. Decommissioning abandoned services, stale accounts, and unnecessary inbound access often eliminates entire classes of vulnerabilities at once.
Supply Chain Visibility: SBOM and VEX
Many organizations now discover vulnerabilities through components rather than first-party code. Supply chain visibility makes vulnerability response faster and less wasteful.
NTIA defines SBOM minimum elements and describes SBOM as a formal record of software components and supply chain relationships.
CISA provides minimum requirements for VEX, which helps communicate whether a specific vulnerability is exploitable in a given product or deployment context, reducing unnecessary remediation work.
Used together, SBOM improves discovery and VEX improves decision quality.
Making Vulnerability Reduction Sustainable
Programs fail when remediation depends on heroics. Sustainable reduction requires operational design:
- Clear ownership for every asset class and every remediation type
- Service-level expectations that match business criticality
- Change windows and automated rollout mechanisms for patches and configuration updates
- Metrics tied to risk reduction, not ticket volume
Useful metrics include time to remediate KEV-listed issues on critical systems, reduction of externally reachable critical weaknesses, and closure rate of repeat misconfigurations.
What Secure by Design Means for Vulnerabilities
Many vulnerabilities persist because products ship insecure by default or require expert hardening to be safe. CISA Secure by Design guidance is intended to shift security responsibility toward manufacturers and to help customers evaluate progress.
For buyers, Secure by Design becomes a procurement lever: demand secure defaults, strong logging, strong authentication options, and clear vulnerability disclosure practices.
Frequently Asked Questions(FAQ)
What is the difference between a bug and a vulnerability?
A bug is any defect that causes incorrect behavior. A vulnerability is a defect or weakness that can be exploited to violate security goals. Not every bug is security-relevant.
Is phishing a vulnerability or a threat?
Phishing is a threat technique. It succeeds by exploiting vulnerabilities in human behavior and business processes, such as weak verification steps or rushed approvals.
How do attackers turn a vulnerability into a breach?
They combine three things: a reachable weakness, a workable exploit path, and a follow-on objective such as credential theft, privilege escalation, lateral movement, or data access. Breaking any link in that chain reduces risk.
What should an organization fix first?
Start with vulnerabilities that are known to be exploited in the wild, especially on externally reachable systems or systems that control identity and access. CISA KEV is a strong starting point for that first filter.
Leave a Reply