The speed of cyber defense has historically lagged behind the speed of attack. In 2024, the IBM Cost of a Data Breach Report highlighted a stark reality. Organizations that extensively deployed artificial intelligence and automation in their security operations centers (SOCs) saved an average of $2.22 million per breach compared to those that did not. This financial metric underscores a tactical truth known to every Chief Information Security Officer. Automation is no longer a luxury for mature teams. It is the only viable method to survive the current threat volume.
Cybersecurity automation involves the use of software to create a system that detects, investigates, and remediates cyber threats with little or no human intervention. It addresses the volume problem where human analysts simply cannot manually process the thousands of alerts generated daily by firewalls, endpoints, and cloud monitors.
Moving Beyond Basic Scripts to Orchestrated Defense
Early automation consisted of simple scripts written by engineers to patch servers or block IPs. Today, the industry relies on Security Orchestration, Automation, and Response (SOAR) platforms. Leading solutions like Palo Alto Networks Cortex XSOAR, Splunk SOAR, and Microsoft Sentinel have transformed this discipline into a centralized nervous system for enterprise cybersecurity.
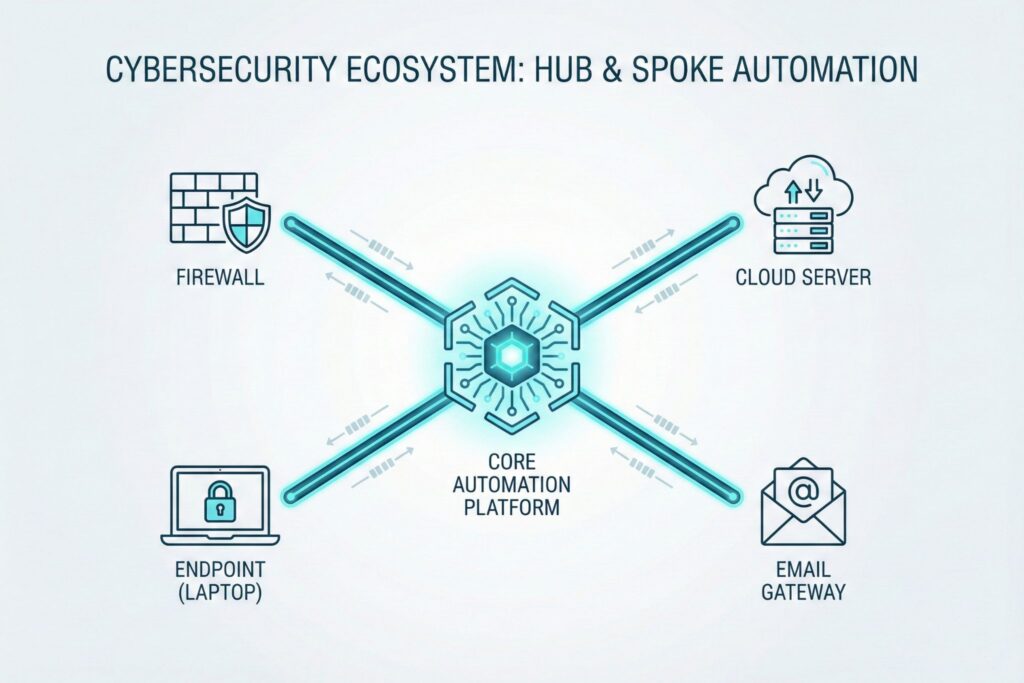
While a SIEM (Security Information and Event Management) system acts as the eyes that see an intrusion, the SOAR platform acts as the hands that stop it. These platforms utilize Application Programming Interfaces (APIs) to stitch together disparate security tools. Instead of an analyst copying an IP address from a log, opening a threat intelligence portal, pasting the IP, and then logging into a firewall to block it, the automation platform executes this entire sequence in milliseconds.
Cybersecurity automation ecosystem diagram showing SOAR platform connected to firewall, endpoint, and cloud via APIs.

Measurable Impact on Response Times and Budget
The primary metric driving cybersecurity automation adoption is the Mean Time to Respond (MTTR). In a manual environment, triaging a single suspicious email can take an analyst 15 to 30 minutes. When multiplied by hundreds of phishing reports a week, this consumes massive amounts of human capital.
Automated workflows reduce this triage time to seconds. This speed does more than save money. It limits the dwell time a cyber attacker has within the network. Reducing the window of opportunity prevents lateral movement and stops data exfiltration before it begins.
The operational difference between manual and automated workflows creates a distinct advantage for modern teams
| Feature | Manual SOC Workflow | Automated SOAR Workflow |
| Initial Action | Analyst notices alert in queue after delay | System triggers playbook immediately upon detection |
| Context Gathering | Manual queries to VirusTotal or internal logs | System instantly enriches alert with threat intel |
| False Positives | Human spends time verifying benign events | Logic engine filters noise without human input |
| Containment | Manual login to firewall or EDR to block | System pushes block rule via API across all devices |
| Scalability | Limited by headcount and shift hours | Scales instantly with alert volume 24/7 |
Anatomy of an Automated Phishing Defense
Phishing remains the most common entry point for cyber attackers and serves as the perfect candidate for automation. In a fully matured environment, a user reports a suspicious email, and the system takes over immediately.
The automation platform parses the email to extract artifacts such as the sender address, subject line, and embedded URLs. It queries global cyberthreat intelligence feeds to check the reputation of these artifacts. If the URL is known to be malicious, the system automatically deletes the email from the inbox of the reporting user and scans the entire organization to delete the same email from other mailboxes. Finally, it updates the email gateway blocklist to prevent future delivery and closes the ticket.
Automated phishing defense workflow diagram: detection, analysis, and remediation steps.
A human analyst only intervenes if the system cannot make a definitive determination.
Strategies to Avoid Automating Chaos
Implementing these cybersecurity systems requires a disciplined approach to avoid operational disasters. A common failure mode occurs when teams attempt to automate a process they do not fully understand. Automating a broken workflow does not fix the workflow. It merely breaks things faster.
Experienced engineers follow a strict rule where no process is automated until it has been manually executed and documented multiple times. This ensures that the decision logic is sound.
Furthermore, false positives present a significant business risk. An aggressive automated rule that blocks a legitimate server based on a traffic spike could inadvertently shut down a customer-facing portal. To mitigate this, successful teams implement a human-in-the-loop strategy. The system performs all the data gathering and recommends an action, but a human analyst must click a button to authorize the final containment step. This hybrid approach balances speed with safety.
The Shift from Static Playbooks to Hyperautomation
As we move through 2025, the definition of automation is evolving due to Generative AI. Traditional automation relies on static playbooks which are rigid logic maps. If an attack does not fit the pre-defined logic, the automation fails.
Newer hyperautomation strategies integrate Large Language Models (LLMs) to interpret ambiguous data. Microsoft Security Copilot and similar tools allow the system to summarize complex incident data in plain English and even suggest new code to update playbooks on the fly. This shifts the SOC from a reactive stance based on static rules to a predictive stance where the automation adapts to the behavior of the attacker.
Organizations that treat automation as a strategic capability rather than a simple IT project position themselves to handle the exponential growth of cyber threats. The goal is not to replace human analysts but to elevate them, allowing machines to handle the data while humans handle the strategy.
FAQ
According to the 2024 IBM Cost of a Data Breach Report, organizations that extensively deploy AI and automation save an average of $2.22 million per breach compared to those without these capabilities. Automation is currently the most effective factor in reducing the total cost of a security incident.
While automation dramatically reduces Mean Time to Respond (MTTR), fully autonomous systems risk disrupting legitimate business operations through false positives. A “human-in-the-loop” strategy mitigates this risk by having the software handle data aggregation and recommendation, while a human analyst authorizes the final high-impact containment actions.
Traditional SOAR relies on static, rigid logic maps that can fail when facing undefined threats. Generative AI enables hyperautomation, allowing the system to interpret ambiguous data, summarize complex incidents, and adaptively update defense logic in real-time, shifting cybersecurity from reactive to predictive.

Leave a Reply