Cybersecurity risk is now a core business risk with measurable financial impact. IBM’s 2024 Cost of a Data Breach Report put the global average cost of a breach at USD 4.88 million, with the mean time to identify and contain a breach at 258 days. Those timelines turn incidents into prolonged disruption through downtime, customer churn, regulatory exposure, and recovery labor.
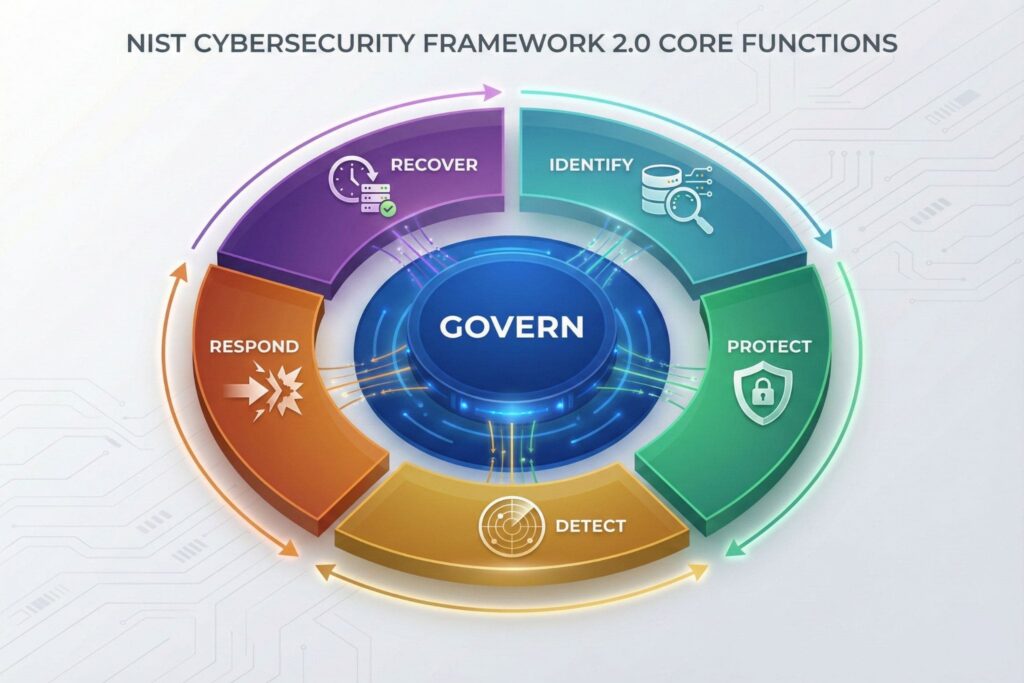
The NIST Cybersecurity Framework CSF 2.0 helps organizations manage that risk in a consistent, repeatable way. NIST released CSF 2.0 in February 2024 and expanded the NIST CSF core model to six Functions by adding Govern. The update strengthens cybersecurity governance and makes the framework easier to use as an enterprise risk management tool. CSF 2.0 is not a prescriptive cybersecurity standard or a control checklist. It is a cybersecurity framework and risk management framework that helps teams describe desired cybersecurity outcomes in plain language, align cybersecurity strategy with business priorities, and connect outcomes to security controls, security policies, and operational evidence.
What the NIST CSF 2.0 Functions Are and How They Work
CSF 2.0 organizes cybersecurity outcomes into six Functions that cover the lifecycle of cybersecurity risk management. The most practical way to apply the NIST Cybersecurity Framework CSF 2.0 Functions is to treat each one as a decision area that produces proof, not as a set of siloed security activities across the security program.
| Function | The Decision It Forces | Evidence That It Exists |
|---|---|---|
| Govern | Who owns cyber risk and how exceptions get approved | Risk appetite statement, policy set, third party requirements, board reporting cadence |
| Identify | What must be protected and what failure would cost most | Service inventory, data classification, dependency map, risk register with owners |
| Protect | Which safeguards are worth the friction and cost | Access design, configuration baselines, secure build standards, training completion evidence |
| Detect | How quickly you can see abnormal activity where it matters | Logging coverage for critical systems, alert triage process, detection rules with review dates |
| Respond | How reliably you can contain and communicate | Incident response playbooks, on call model, escalation paths, tabletop results, forensics readiness |
| Recover | How fast the business can resume acceptable operations | Restore test results, recovery objectives, post incident fixes, resilience backlogs |
Two breach signals underline why Govern is central to NIST CSF 2.0 implementation. Verizon reports the human element was a component of 68 percent of breaches, which points to policy, accountability, and security culture as much as technical configuration. Verizon also reports ransomware was present in 32 percent of breaches and a top threat across 92 percent of industries. Governance determines whether supply chain risk management, access control discipline, security awareness training, backup testing, and incident response readiness are treated as funded requirements rather than optional projects.
Profiles That Match Business Reality
Profiles are the mechanism that turns the NIST Cybersecurity Framework from an abstract model into an operating plan. NIST describes Organizational Profiles as a way to express current and target posture in terms of CSF outcomes. A high quality CSF Profile starts with segmentation because not every system, application, or business service carries the same operational risk.
Use a service lens instead of an asset lens. Pick one business service that has clear owners and measurable impact, such as customer identity and access management, payment processing, order fulfillment, healthcare operations, or a core SaaS platform. Then define a Current Profile using evidence. If you cannot prove an outcome through telemetry, audits, tests, or process artifacts, treat it as not achieved. This rule reduces ambiguity and forces evidence based cybersecurity maturity work within a CSF implementation.
A practical Profile document can stay short while remaining complete.
| Field | What It Contains |
|---|---|
| Service scope | The user facing service boundary and its dependencies |
| Impact statement | What stops working, who is harmed, and how fast |
| Current outcomes | CSF outcomes you can demonstrate today |
| Target outcomes | Outcomes justified by impact and risk tolerance |
| Gaps and owners | Missing outcomes with a named accountable owner |
| Evidence plan | What logs, tests, or artifacts will prove closure |
Profiles improve communication between security teams and leadership. Instead of debating tools, teams debate risk, impact, and outcomes. That change makes cybersecurity investment discussions clearer and reduces rework because success criteria are defined upfront.
What NIST CSF 2.0 Tiers Mean for Cybersecurity Maturity
CSF Tiers describe how an organization manages cybersecurity risk, not whether it is secure. NIST presents the NIST Cybersecurity Framework CSF 2.0 as adaptable to mission needs and risk appetite, which is why Tier selection should vary across services and business units.
Treat Tiers as a planning dial that helps link cybersecurity maturity to business criticality.
- Tier 1 Partial fits environments where practices are ad hoc and visibility is limited.
- Tier 2 Risk Informed fits teams with approved practices but uneven execution.
- Tier 3 Repeatable fits standardized processes with consistent application.
- Tier 4 Adaptive fits continuous improvement driven by lessons learned and threat awareness.
If a low impact internal tool is Tier 2, that may be a rational risk decision. If identity, payments, or customer data systems remain Tier 2, the organization may be accepting avoidable exposure. The Tier discussion becomes valuable when it produces a decision on investment, owners, target dates, and measurable outcomes in the cybersecurity program.
Metrics That Prove Risk Reduction
Boards do not need a catalog of blocked attacks. They need evidence that exposure is shrinking and incident response is improving. IBM’s breach lifecycle finding of 258 days to identify and contain is a useful benchmark because it translates security performance into time based loss duration.
A compact cybersecurity metrics scorecard can cover outcomes across the lifecycle, using operational metrics that map to NIST CSF 2.0 Functions and support cybersecurity risk management reporting.
| Function | Metric | What Good Looks Like |
|---|---|---|
| Govern | Exception rate with time bound approvals | Few exceptions, all time limited, recurring exceptions trigger design change |
| Identify | Coverage of critical services in inventory | Every critical service has an owner, dependency map, and reviewed impact |
| Protect | Patch compliance for critical vulnerabilities | Most critical fixes meet the agreed service level for high impact systems |
| Detect | Time to acknowledge high severity alerts | Fast acknowledgment on critical systems with clear escalation |
| Respond | Time to contain priority incident types | Predictable containment for the most likely scenarios |
| Recover | Restore test pass rate and recovery objective adherence | Regular restore tests with documented results and fixes tracked |
To keep metrics honest, tie each one to an evidence source that cannot be gamed easily. Examples include automated restore logs, immutable ticket trails for incident handling, configuration compliance reports, and detection coverage summaries for crown jewel systems.
How to Implement the NIST Cybersecurity Framework CSF 2.0 in 90 Days
Start small and finish measurable. A focused rollout is the fastest path to operationalizing the NIST Cybersecurity Framework CSF 2.0 framework and building a sustainable security program.
- Choose one critical service and publish ownership for risk decisions under Govern, including how security exceptions are approved.
- Build a Current Profile using evidence and list the top five outcome gaps with named owners.
- Set a Target Profile that reflects impact rather than ambition and align it with a Tier choice for that service.
- Map gaps to initiatives that produce proof, such as logging coverage, restore testing, supply chain requirements, vulnerability management, and incident response playbooks.
- Report a monthly scorecard with three to five metrics and a short narrative of what changed, what is blocked, and what risk was reduced.
This sequence makes CSF 2.0 feel less like documentation and more like a cybersecurity risk management system that improves detection, containment, and recovery outcomes.
Common Failure Patterns and How to Avoid Them
The first failure pattern is identical Targets for every system. It wastes budget and hides real priorities. The fix is segmentation based on business impact and threat exposure.
The second is activity lists with no accountable owner in Govern. Without decision rights and ownership, gaps persist even when security tools exist. The fix is to publish governance, accountability, and exception handling early as part of the CSF 2.0 rollout.
The third is treating evidence as an audit afterthought. Evidence is the product of implementation. If the organization cannot prove logging coverage, restore reliability, secure configuration baselines, or incident response readiness, it should assume the opposite and plan accordingly.
The NIST Cybersecurity Framework CSF 2.0 works in 2025 when it is used to make defensible decisions, backed by verifiable evidence, and tracked with metrics that reflect business outcomes rather than tool activity.
Frequently Asked Questions (FAQ)
The addition of the sixth function, Govern, which elevates cybersecurity from a technical IT responsibility to a comprehensive enterprise risk management issue requiring active senior leadership involvement.
No, your existing controls remain valid, but you must now explicitly map how your strategy, policy, and supply chain decisions support those controls under the new Govern function.
It shifts the conversation from purchasing technical tools to agreeing on “Target Profiles” and “Tiers,” allowing the Board to fund specific business outcomes and risk acceptance levels rather than just security software.
While technically voluntary, it has become the de facto standard of care used by cyber insurance providers to determine premiums and by legal teams to assess liability after a breach.
Stop trying to fix the whole organization at once; instead, create a Current and Target Profile for one single critical business service (e.g., payments or customer identity) to prove risk reduction.
Leave a Reply