IoT cybersecurity fails most often for a simple reason. Devices arrive faster than organizations can inventory, segment, and govern them. IoT Analytics estimated 18.5 billion connected IoT devices in 2024 and projected 21.1 billion by the end of 2025, which means more endpoints, more firmware versions, and more unknown owners inside the cyber perimeter.
The risk is rarely the sensor itself. The risk is the path it creates. A camera, badge reader, smart display, or HVAC controller becomes a quiet foothold, then a pivot point into systems that actually matter. Cybersecurity teams usually discover this when a device starts speaking to destinations it has no business contacting or when a vendor cloud account becomes the weakest link.
What follows is a practical cybersecurity program for addressing IoT security challenges in offices, warehouses, retail, and mixed IT and OT environments. It prioritizes actions you can verify and maintain, not theory.
Cybersecurity Starts With Visibility
Treat IoT as a fleet with owners, routes, and replacement dates. If you only do one thing this week to address IoT security challenges, make unknown devices visible and assign responsibility. The fastest path is network visibility, not agents on endpoints.
Use the networks you already control. DHCP leases, DNS logs, Wi Fi controller lists, switch MAC tables, and firewall egress logs will show what is present and what it is trying to reach. Once you have a first pass, tag every device with an owner who can answer one question. What business process breaks if this device is isolated.
A small change here improves everything else. Cyber alerts become actionable because they map to a person. Cybersecurity segmentation rules become stable because they map to a function.
Why Defaults Still Break IoT Security in 2025
Attackers still look for the easiest path into cyber networks. Mirai is the classic illustration because it scaled by scanning exposed services and attempting logins using a short list of common default usernames and passwords. CISA documented Mirai using a list of 62 common default username and password pairs to compromise vulnerable IoT devices.
The exact malware family changes, but the pattern does not. Internet reachable management interfaces, weak credentials, and forgotten devices remain profitable.
Regulators have started turning these lessons into baseline cybersecurity expectations. The UK consumer connectable product security regime came into effect on 29 April 2024 and includes requirements that address default passwords and vulnerability reporting contacts. Even if you operate outside the UK, these requirements are a useful benchmark for supplier conversations because they are specific and testable.
Cybersecurity Identity and Access That Survive Operations
IoT device identity needs to survive real life. Devices move between sites. Contractors install them. Networks change. If identity is a one time setup step, it will decay.
Focus on three cybersecurity controls that scale.
First, eliminate shared credentials and require unique credentials for any interactive management access. Second, restrict management to dedicated admin networks and remove it from user VLANs. Third, use certificate based identity for device to network authentication where feasible, especially for device classes that are numerous and cyber sensitive such as cameras, access control, and building systems.
You do not need perfection across every device class on day one. You need a standard onboarding path that new devices must follow and a revocation path that works when devices are moved, replaced, or returned.
Segmentation That Contains Breaches
Cyber segmentation is not only about separating IoT from laptops. It is also about controlling where IoT can go. Most IoT devices need a narrow set of destinations such as DNS, NTP, a vendor cloud endpoint, and a management platform.
Make cyber egress control explicit. If you only isolate with VLANs but allow unrestricted outbound internet, compromise still becomes a cyber data exfiltration and command and control problem.
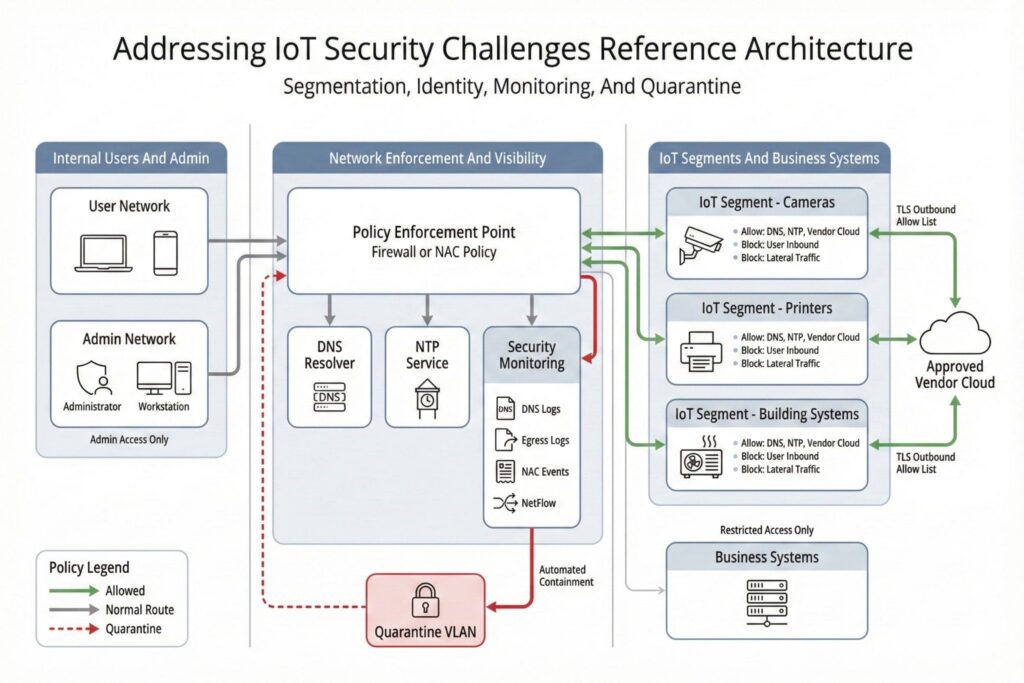
The table below shows a practical approach you can implement with VLANs plus firewall rules or NAC based cyber policy.
| Device Class | Allowed Destinations | Blocked Paths | Alert Signal |
|---|---|---|---|
| Cameras | DNS NTP approved vendor cloud | User VLAN inbound lateral traffic | New destination domain or country |
| Printers | Print servers DNS NTP | Direct internet outbound | Outbound TLS to unknown hosts |
| Smart Displays | Content platform DNS NTP | Admin consoles from user VLAN | New ports or protocols |
| Building Systems | BAS servers DNS NTP | Internet inbound user VLAN access | East west traffic spikes |
IoT Cybersecurity You Can Govern
Patch management fails for IoT when updates are unclear, unsafe, or operationally painful. Build cybersecurity governance around what you can verify.
Require suppliers to state an end of support date and an update method that can be performed safely. If the device cannot be updated without risky downtime or the vendor does not commit to a support window, you are not buying hardware, you are buying an ongoing cyber exception.
NISTIR 8259 emphasizes that manufacturers can help customers by providing necessary device cybersecurity capabilities and cybersecurity related information. Use that framing in procurement so requirements stay tied to capabilities, not marketing promises.
A simple device record prevents future chaos and supports cyber governance.
| Field | What Good Looks Like |
|---|---|
| Owner | Named team and escalation contact |
| Location | Site building room or rack |
| Model and Firmware | Exact identifiers that match vendor advisories |
| Connectivity | Wi Fi wired cellular and network segment |
| Update Method | Console OTA management platform and rollback plan |
| Support Window | End of support date and expected cadence |
Detection That Works With Constrained Devices
Many IoT devices produce limited logs. Some speak unusual protocols. Others are managed by third parties. Assume endpoint telemetry will be thin and design cyber detection around the network.
Prioritize signals that are hard for attackers to hide and easy for cyber teams to route to triage.
- New outbound destinations for a device class that normally talks to a fixed set of endpoints
- New listening services on an IoT segment
- Repeated authentication failures against device admin interfaces
- East west traffic between IoT devices that normally do not communicate
Do not turn this into a monitoring vanity project. The goal is fast cyber containment.
Cyber Incident Containment Without Downtime
IoT cyber containment is not always isolation of a single endpoint. Some devices cannot be taken offline. Some are safety relevant. Your playbook must reflect that.
Use this sequence as a default and adjust for OT and safety critical classes.
- Confirm whether the device is required for safety or essential operations and identify the owner
- Quarantine at the network layer by tightening egress and blocking lateral traffic while preserving required functions
- Capture network indicators and current configuration state for investigation
- Reset or reimage only when you have a secure re onboarding path
- If the device is outside its support window, plan replacement and treat the old unit as a controlled cyber exception until removed
A Minimal IoT Cybersecurity Scorecard That Drives Decisions
The most common failure is buying devices that cannot be governed. Make cybersecurity purchasing decisions measurable.
Verizon’s 2025 DBIR found credential abuse at 22 percent and exploitation of vulnerabilities at 20 percent among leading initial attack vectors, and reported a 34 percent surge in vulnerability exploitation. Those numbers should push two procurement requirements to the top. Unique credentials and a supported update path.
Translate that into contract language you can test. Require a vulnerability disclosure process, a support period, a patch delivery mechanism, and a point of contact for security reports. The UK regime is a practical reference point because it forces clarity on defaults and reporting contacts.
A Minimal IoT Cybersecurity Scorecard That Drives Decisions
The best IoT cybersecurity metrics are few, trendable, and tied to actions. Track only what changes cyber risk and budget choices.
| Metric | Target Direction | Decision It Enables |
|---|---|---|
| Devices with Assigned Owners | Up | Faster triage and fewer unknowns |
| IoT Segments with Egress Allow Lists | Up | Reduced command and control space |
| Devices Within Vendor Support Window | Up | Replacement planning and fewer exceptions |
| Time to Quarantine an IoT Incident | Down | Reduced blast radius and downtime |
When these trends move the right way, your program becomes defensible. You can show what improved, why it improved, and what the next investment will buy.
Addressing IoT security challenges in cybersecurity is not solved by a single tool. It is solved by visible ownership, constrained routes, verified update support, and a containment plan that respects operations. The organizations that get this right treat devices as managed assets from purchase to retirement and make the network do the heavy lifting where endpoints cannot.
Frequently Asked Questions (FAQ)
Assign ownership to the team that relies on the device to keep a business process running. Ownership should include an escalation contact and authority to approve isolation during an incident. If no team accepts ownership, treat the device as nonessential and restrict it until a business owner is identified.
Keep the device on an IoT segment and allow outbound traffic only to the specific services it needs, such as DNS, NTP, and approved vendor cloud endpoints. Block inbound access from user networks and block lateral device to device traffic by default. Alert on new destinations, new ports, or traffic to unfamiliar regions.
Treat it as a risk that must be contained, not a normal asset. Reduce exposure by tightening egress, removing unnecessary services, and limiting management access to controlled networks. Set a replacement date and track it as an exception that requires periodic review.
Look for network level changes that do not fit the device class baseline. Common signals include new outbound destinations, unexpected listening services, repeated login failures against management interfaces, and unusual east west traffic within IoT segments. Use these signals to trigger quarantine actions that preserve essential functions while stopping spread.

Leave a Reply