Author: Alex Mercer – Principal Security Architect specializing in cloud infrastructure defense and enterprise cyber risk mitigation.
TL;DR: Business and security teams often confuse attack vectors (the how) with attack surfaces (the where). Knowing the difference is crucial for prioritizing fixes. This guide breaks down both concepts using real-world incident response experience to help you minimize exposure without breaking business workflows.
Clarifying Cybersecurity Terminology: Vector vs. Surface
In our work assessing enterprise risks, I frequently see teams confuse attack vectors with attack surfaces. This confusion makes it difficult to prioritize security fixes and communicate threats to leadership effectively. Let’s clear this up with actionable strategies to minimize your exposure.
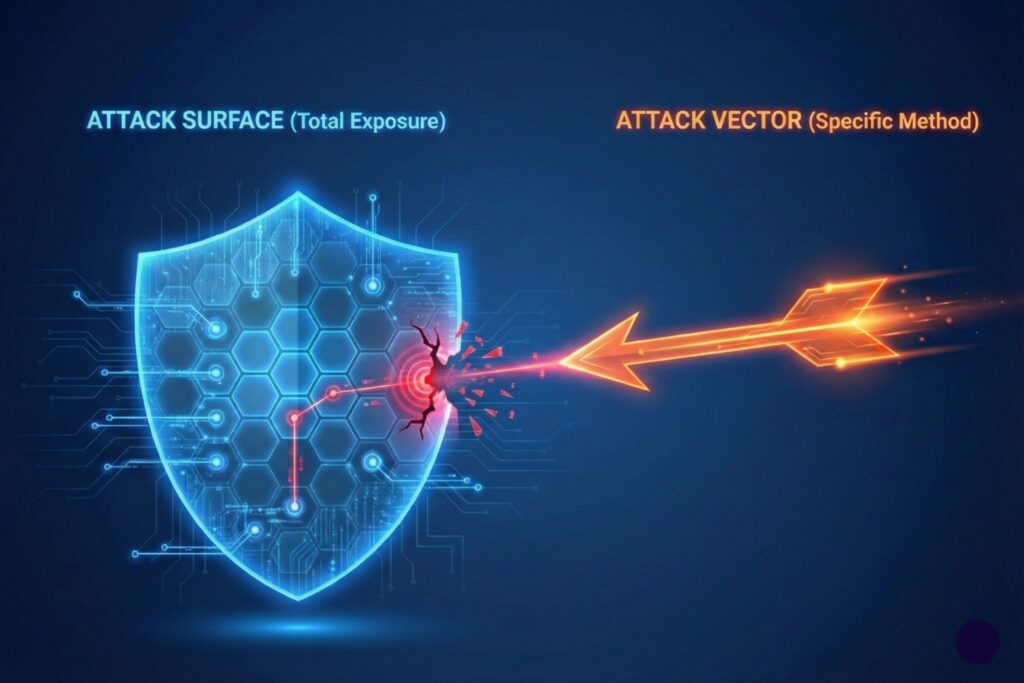
According to the National Institute of Standards and Technology (NIST), an attack surface represents all points where unauthorized users can interact with your system. An attack vector represents the specific method or pathway hackers utilize to exploit those vulnerable points.
You can think of the surface as your exposed perimeter and the vector as the tool used to breach it. Understanding this distinction is fundamental for building resilient digital environments.
How Vectors Expand Surface In Incidents
Cyber incidents usually begin when a specific vector targets a weakness on your attack surface. The compromised surface area then expands rapidly as the attacker gains deeper access into your network.
Let me share a scenario my team handled recently. An employee received a deceptive invoice email and entered their credentials into a fraudulent authentication portal. We quickly noticed unusual login locations and repeated multi-factor authentication (MFA) requests.
- The Initial Vector: Credential phishing.
- The Affected Surface: The identity provider and mailbox rules.
We acted by revoking sessions and restricting forwarding rules to prevent lateral movement. Failing to distinguish between these elements during a post-incident review leaves critical vulnerabilities unpatched. Focusing only on the phishing method might cause you to overlook overly permissive access policies. A comprehensive defense strategy must address both the entry method and the exposed assets.
A Simple Vector To Surface Map
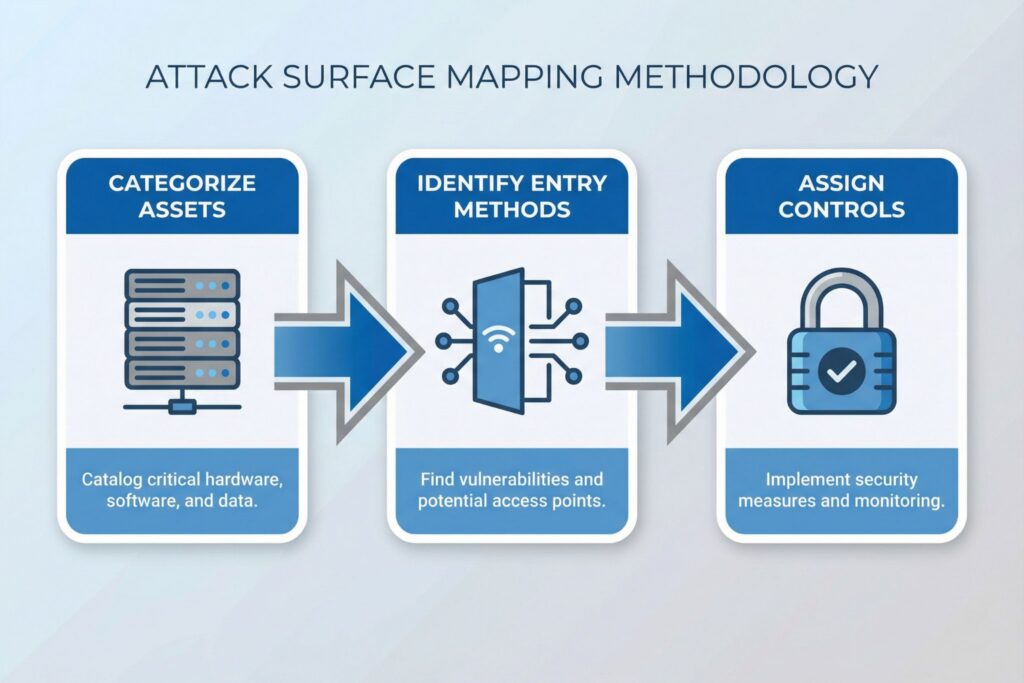
Security teams operate much faster when they link common entry methods to the specific environmental components that create risk. The resulting documentation should be highly accessible for both engineering departments and executive leadership.
Establishing a concise list of pairings ensures every vulnerability has a designated owner and a verifiable security check. Assuming a hybrid environment with cloud identity providers and remote administration tools, here is a practical mapping process:
- Start with dynamic categories such as external services and vendor connections.
- List only the realistic entry methods that apply to each specific category.
- Validate your findings using concrete configuration evidence rather than theoretical brainstorming.
- Assign exactly one control owner and one verifiable artifact for every identified pairing.
Reducing Your Attack Surface
Attack surface reduction essentially requires highly disciplined exposure management. The primary objective is minimizing reachable paths to critical assets rather than simply eliminating systems. You must implement these security improvements without disrupting essential business workflows.
In my experience, organizations achieve the best results by adopting a change-friendly approach:
- Inventory all internet-facing services and remove obsolete DNS records immediately.
- Reduce standing privileges and restrict high-risk authentication methods within your identity infrastructure.
- Establish secure baselines for endpoints and separate administrative workstations from general web browsing.
- Review third-party application permissions and enforce the principle of least privilege across cloud environments.
Reducing exposure often fails when security teams break existing processes without providing a clear exception mechanism. You need a reliable framework that allows temporary waivers with strict compensating controls. Disabling legacy authentication might disrupt a vital integration if you do not plan the migration carefully. Treating that integration as a known risk with stringent network scoping allows business operations to continue safely.
Control Sets For Common Entry Paths
Managing threats becomes significantly easier when you categorize them into repeatable control sets instead of treating them as isolated problems. These control sets must directly support your prevention and detection capabilities. The strategies outlined here apply seamlessly to modern corporate infrastructures utilizing cloud software and remote access.
Prioritizing these areas systematically strengthens your overall security posture against sophisticated adversaries:
- Deploy phishing-resistant MFA and enforce strict conditional access policies based on device trust.
- Limit remote access enrollment to authorized personnel and monitor for unusual administrative sessions continuously.
- Apply rigorous patch management and baseline hardening for all externally reachable systems.
- Mandate isolated connection pathways and conduct periodic access reviews for all external vendors.
Technical teams should tie every identified vector to existing telemetry and specific automated response actions. The MITRE ATT&CK framework provides an excellent catalog of adversary behaviors to guide your detection engineering. Leveraging this structured approach ensures your threat hunting covers the most likely attack scenarios.
Key Metrics for Measuring Attack Surface Reduction
Executive leaders require tangible proof that exposure reduction efforts actually protect the business. Security practitioners equally need actionable metrics that drive intelligent technical decisions rather than generating meaningless dashboards.
You should run and analyze these checks over an eight-week operational cycle to identify meaningful trends. Effective metrics must include precise scopes and definitive thresholds to remain useful:
- Track the total count of externally reachable services and cloud applications possessing high-privilege consent.
- Measure the percentage of administrative actions performed exclusively from hardened and monitored endpoint devices.
- Calculate the median time required to remediate critical vulnerabilities on internet-facing infrastructure completely.
- Monitor the alert-to-triage timeframe for high-severity events while accounting for approved policy exceptions.
Accountability requires explicit ownership assignments. Infrastructure and application teams typically own the attack surface, while security personnel validate the corresponding evidence. You must convert post-incident findings into a prioritized backlog featuring named owners and strict deadlines. This cooperative dynamic ensures continuous improvement and prevents identical breaches from occurring twice.
Frequently Asked Questions (FAQ)
External assets represent a high-priority subset, but the total surface includes many internal pathways. Internal identity systems and APIs become vulnerable targets once an attacker breaches the perimeter.
Absolutely. A single successful credential phishing campaign frequently unlocks access to email accounts and cloud administrative consoles simultaneously. Each compromised area requires distinct security controls.
Small teams must prioritize identity management and external exposure reduction above all else. Tightening sign-in policies and identifying exactly what assets are reachable from the public internet prevents easy external compromises without demanding a massive enterprise security budget.
Describe the surface as your reachable business assets and the vector as the hacker’s break-in method.
The framework focuses primarily on categorizing specific adversary behaviors and technical exploitation techniques. Translating these behavioral patterns helps organizations build comprehensive detection rules across their entire network.
Leave a Reply