Author: Dana Marlowe — technology writer and editor with over ten years of experience covering cybersecurity, privacy, and enterprise IT. Has contributed to security-focused publications and worked directly with IT and compliance teams across regulated industries.
Consultant: Marcus T. Reid, CISSP, CEH — certified cybersecurity professional with 14 years of experience in network security architecture, vulnerability management, and enterprise threat detection. Has designed and audited UTM deployments for organizations in financial services, healthcare, and manufacturing.
When a ransomware payload reaches a company’s network, the failure is rarely one tool missing — it’s usually that no single tool was watching the right layer at the right time. Unified Threat Management, or UTM, exists to close that coordination gap. Instead of running a firewall from one vendor, an intrusion detection system from another, and antivirus software from a third, UTM combines those functions into one appliance or cloud-hosted service. For organizations without a dedicated security operations team, that consolidation changes what’s actually manageable day to day.
How UTM Bundles Network Security Functions
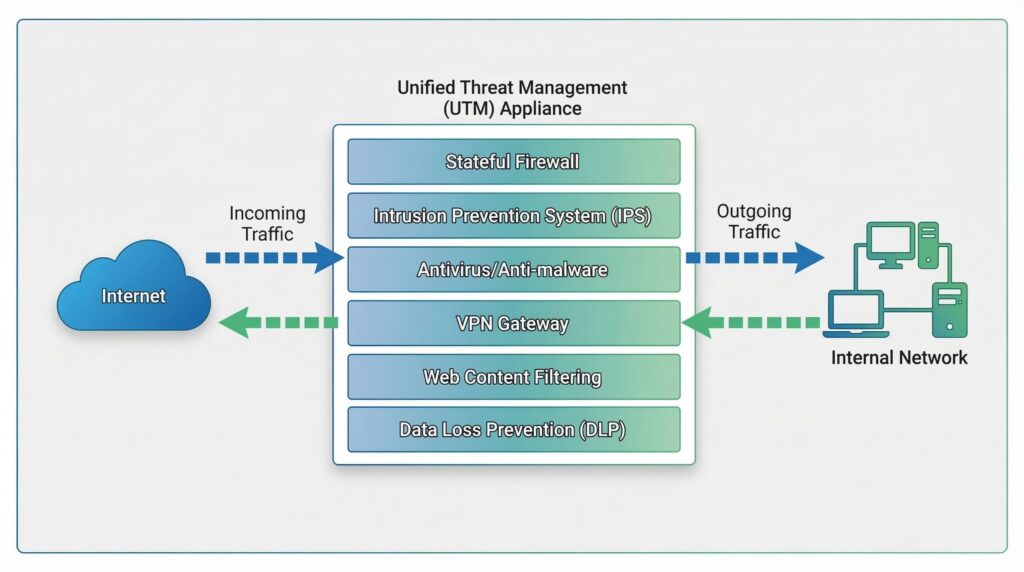
A UTM platform sits at the network perimeter — between the internal network and the internet — and inspects traffic flowing in both directions. A typical deployment includes a stateful firewall, an intrusion prevention system (IPS) that scans traffic for known attack signatures and blocks suspicious activity in real time, antivirus and anti-malware filtering, virtual private network (VPN) support for encrypted remote connections, and web content filtering that checks destinations against databases of malicious domains before a browser ever loads them. Some platforms also include data loss prevention tools that flag or block sensitive data from leaving the network without authorization.
The practical appeal for smaller organizations is hard to overstate. The Verizon Data Breach Investigations Report 2024 found that organizations with fewer than 1,000 employees accounted for a substantial share of confirmed breaches, yet those same organizations rarely have the IT staff to operate complex, multi-vendor security environments. A single UTM appliance reviewed from one dashboard addresses that gap directly.
Marcus Reid, a certified cybersecurity professional with 14 years of experience auditing and designing network security deployments across healthcare, financial services, and manufacturing, puts it plainly: in environments where one administrator is responsible for everything from patch management to endpoint support, the value of UTM isn’t the technology itself — it’s the reduction in cognitive load that comes from not switching between three separate consoles to understand a single incident.
What Runs Inside a UTM Appliance
Deep Packet Inspection and Hardware Sizing
What separates UTM from a basic firewall is deep packet inspection, or DPI. A standard firewall examines the header of a network packet — the source and destination addresses — and makes a pass-or-block decision. DPI looks inside the packet’s actual content, which allows the system to detect malware concealed in otherwise legitimate-looking traffic and identify applications attempting to disguise themselves as standard web browsing.
DPI is computationally intensive. When a vendor publishes a throughput figure for a UTM appliance, that number typically reflects performance without all security modules active. Fortinet, for example, publishes separate throughput ratings for firewall-only versus full threat protection in its FortiGate datasheets — the difference can exceed 60 percent on mid-range models. Reid notes that hardware undersizing at purchase is the most common operational problem he encounters in UTM audits: organizations buy at minimum specification, then find performance degrading within 18 months as traffic volume grows and additional modules are switched on.
Centralized Logging and Incident Response
Because all security functions run through one platform, UTM produces a unified event log. Rather than manually correlating firewall events with separate IPS alerts and a third antivirus report, an administrator sees one activity stream. That centralized visibility shortens the time between an event occurring and someone noticing it — which matters considerably given that the median time to detect a breach in smaller organizations frequently extends to weeks (IBM Cost of a Data Breach Report 2024).
How UTM Compares to Next-Generation Firewalls
The distinction between UTM and next-generation firewalls (NGFW) is genuinely blurry, and several major vendors now market the same hardware under both labels depending on configuration. The practical difference tends to come down to deployment scale. NGFWs are generally engineered for high-throughput enterprise environments where performance under full inspection load cannot be compromised, and they integrate more tightly with security information and event management (SIEM) platforms and external threat intelligence feeds. UTM products are positioned for smaller environments where consolidated management and cost efficiency matter more than raw throughput.
The table below captures the most relevant differences for a decision-maker choosing between the two:
| UTM | NGFW | |
|---|---|---|
| Typical deployment size | Up to ~500 seats | 500 seats and above |
| Primary priority | Consolidated management, cost efficiency | Throughput, performance under load |
| SIEM and threat intelligence integration | Basic or optional | Native, deeply integrated |
| Approximate entry price | $500–$3,000 (hardware appliance) | $5,000–$30,000+ |
| Managed by | Single generalist administrator | Dedicated security team or SOC |
NIST Special Publication 800-41, which remains the foundational federal guidance on firewall policy and classification, deliberately avoids prescribing specific product categories — its value here is definitional rather than prescriptive, and organizations should evaluate any perimeter security tool by its actual functional capabilities rather than its marketing label (NIST SP 800-41 Rev. 1, 2009).
One development worth acknowledging: cloud-native security architectures, particularly Secure Access Service Edge (SASE), are increasingly discussed as an alternative to on-premise UTM appliances for distributed teams. Whether SASE makes UTM obsolete depends entirely on organizational size, cloud adoption maturity, and budget — for many sub-500-seat organizations, UTM remains the more practical and affordable perimeter solution by a significant margin.
When UTM Decisions Need a Professional
Organizations operating under HIPAA or PCI DSS need to verify that their UTM solution meets specific logging, access control, and encryption standards — this is not a detail to resolve after deployment. Reid recommends treating compliance requirements as a filter applied before vendor selection, not an afterthought.
One function with direct compliance implications is SSL/TLS inspection, which many UTM platforms support. This feature temporarily decrypts HTTPS traffic, scans it for threats, and re-encrypts it before forwarding. It is one of the more effective ways to catch malware delivered over encrypted connections — but it requires a trusted certificate to be installed on end-user devices and, depending on jurisdiction and industry, can raise legal and privacy questions about employee or customer data. Under GDPR, for instance, decrypting employee communications may require specific legal basis and policy disclosure. This decision warrants legal review before the feature is enabled, not after.
If your team lacks experience interpreting security logs, tuning IPS rules, or responding to alerts, professional help is the right call. Misconfigured UTM policies are a common source of both security gaps and unnecessary service disruptions. A managed security service provider can handle initial configuration, ongoing monitoring, and incident response while internal staff focus elsewhere.
What UTM Cannot Do
UTM is not a substitute for a complete security posture. No perimeter defense stops threats that originate inside the network — a compromised employee credential, a misconfigured internal server, or a malicious insider all bypass perimeter controls entirely. Endpoint protection, security awareness training, and regular vulnerability management remain necessary alongside UTM, not optional additions to it.
An appliance running at default configuration without regular log review, signature updates, and policy audits provides perimeter coverage in name only. Threat signatures should update automatically and frequently — new malware variants emerge daily. Firmware updates from the vendor should be applied promptly, as they often patch vulnerabilities in the UTM platform itself.
Choosing UTM is less a one-time purchase decision than an ongoing operational commitment. The organizations that get the most from it are those that treat maintenance as part of the deployment, not something to revisit when a problem appears.
Frequently Asked Questions(FAQ)
It can be, but the economics depend on whether a full UTM appliance is warranted versus a modern business-grade router with built-in threat filtering. The key question is whether the organization handles sensitive client data or faces regulatory requirements — if yes, a proper UTM deployment is worth the investment. If not, simpler options may provide adequate coverage at lower cost and complexity.
For most small to mid-sized organizations, yes — UTM includes stateful firewall functionality as a core component. Very large or high-throughput environments may still benefit from a dedicated enterprise firewall, but below the enterprise tier, a properly sized UTM appliance typically handles perimeter firewall duties without issue.
Many UTM platforms support SSL/TLS inspection, which decrypts HTTPS traffic, scans it, and re-encrypts it before forwarding. This is effective but carries privacy and legal implications depending on your industry and region. It requires a trusted certificate on end-user devices and should not be enabled without a policy review and, in regulated industries, legal sign-off.
It depends heavily on hardware. DPI and SSL decryption are the most resource-intensive functions, and vendors typically publish separate throughput ratings for full threat protection versus firewall-only mode — the gap is often 40 to 60 percent on mid-range appliances. Sizing the appliance above your current traffic load, with room to grow, is more reliable than buying at minimum specification.
They operate at different layers. Antivirus software protects individual devices from malicious files. UTM operates at the network level and inspects traffic before it reaches any device. Both are necessary — UTM catches threats at the perimeter while endpoint protection handles anything that gets through or originates on the device itself.
When no one on the internal team has experience reading security logs, writing firewall rules, or responding to IPS alerts. A UTM appliance left to default settings with alerts going unreviewed is not a security control — it’s a false sense of one. Managed services exist precisely for organizations that need the protection but not the in-house expertise to run it.

Leave a Reply