Cyber risk mitigation is the set of decisions and actions that reduce the likelihood of a cyber incident, reduce the impact when an incident occurs, or improve recovery so the business can keep operating. Mitigation is not a report and not a collection of tools. It is the part of cybersecurity work that changes outcomes in production systems.
A practical definition helps teams avoid busywork. If a change makes an attacker’s path harder, reduces the blast radius, shortens containment time, or improves restore reliability, it counts as cyber risk mitigation. If it only produces documentation without changing exposure, access, or recovery, it does not.
Mitigation also assumes tradeoffs. No organization eliminates all risk. The job is to reduce the risks that matter most, prove that they went down, and make residual risk explicit so leadership can own it rather than inherit it.
Risk Treatment Options In Cyber Risk Mitigation
Most organizations use four risk treatment options even when they do not label them formally:
- Reduce risk by lowering likelihood, lowering impact, or both
- Avoid risk by retiring a system, disabling a risky feature, or changing a process
- Transfer risk through insurance, contracts, and supplier obligations
- Accept risk with a named owner, a rationale, compensating controls when possible, and a review date
Ownership is the hinge. Cybersecurity teams can prioritize and verify, but system owners control timelines, budgets, and operational tradeoffs. Mitigation becomes real only when it is assigned to the people who can change configurations, ship code, and approve downtime.
Why Cyber Mitigation Pays Off
Executives fund cyber risk mitigation for one reason. It protects business outcomes. The financial baseline remains sobering. IBM’s 2024 Cost of a Data Breach research reported a global average breach cost of USD 4.88 million, up from USD 4.45 million the prior year. The point is not the exact average for your sector. The point is that a single incident can wipe out a year of security improvements if recovery is weak and decision making is slow.
The operational signal is equally clear. Verizon’s 2024 DBIR reported that the human element was a component in 68 percent of breaches. The same report noted ransomware or extortion was involved in roughly a third of breaches and appeared as a top threat across most industries. In practice, this pushes mitigation toward identity controls, safer defaults, and recovery discipline rather than one-time awareness campaigns.
Strong mitigation also protects delivery speed. Teams that know which cyber risks are highest avoid the cycle of emergency patching, rushed audits, and reactive incident work that hijacks planned projects. Mitigation priorities reduce surprises, which is what most organizations experience as security friction.
Prioritizing Cyber Risk Mitigation Work That Matters
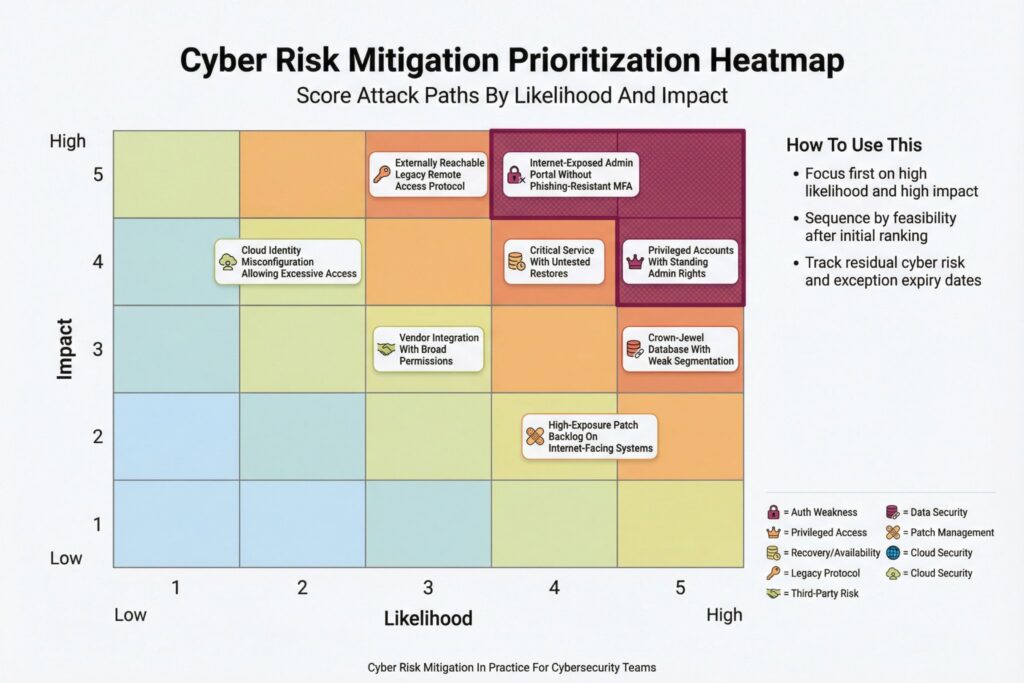
Mitigation programs rarely fail from lack of ideas. They fail when everything is treated as equally urgent. A workable prioritization model stays explainable, resists debate over tiny scoring differences, and links directly to an execution queue with owners and deadlines.
Use three dimensions that non-security leaders can understand.
| Dimension | What You Measure | Examples of Signals | How It Changes Decisions |
|---|---|---|---|
| Likelihood | How plausible the attack path is | Internet exposure, weak authentication, known exploited patterns, reachable admin surfaces | Drives urgency and sequencing |
| Impact | How bad the outcome is | Revenue disruption, safety impact, regulated data exposure, customer trust loss | Drives leadership attention |
| Feasibility | How fast risk can be reduced | Patch exists, config change available, control already deployed, safe rollout path | Drives what you do next |
Keep separate queues for incompatible objects. A strategic concentration risk in third-party services should not compete in the same list as individual software vulnerabilities. Run distinct backlogs for vulnerabilities, identity, third-party risk, and resilience. Then roll up a small set of top items per category to a single executive view.
One technique that reduces arguments is to score the attack path rather than the finding. A critical vulnerability on an internal-only system with no reachable path may be less urgent than a medium severity issue on an internet-facing admin endpoint. Mitigation should follow exposure and exploitability, not labels.
Controls That Change Common Attack Paths
Broad control catalogs look impressive and underperform. Faster risk reduction usually comes from a short set of measures applied consistently, especially across identity, exposure reduction, and recovery.
- Remove unnecessary internet exposure, especially admin interfaces and legacy remote management protocols
- Use phishing-resistant authentication for privileged access and high-impact systems
- Reduce privilege scope and remove standing admin rights where feasible
- Patch based on exploitability and exposure, including known exploited vulnerabilities when they apply to your environment
- Segment networks and services to limit blast radius and lateral movement
- Validate backups through restore tests and protect backup infrastructure from tampering
Depth matters more than coverage. A half-deployed control creates exceptions that attackers exploit and operators learn to work around. Define done in a way that can be verified.
| Control Area | Done Means | Evidence You Can Collect |
|---|---|---|
| Privileged authentication | Strong authentication enforced for privileged accounts on critical systems, exceptions time-bound | Coverage percentage, exception register, authentication logs |
| Exposure reduction | Admin surfaces not reachable from the public internet unless explicitly approved | External attack surface scans, firewall rules, service inventory |
| Patching for high exposure | Remediation deadlines tied to exploitability and exposure, not only severity | Age of exposed findings, patch deployment reports |
| Segmentation | High-impact services have boundaries that limit lateral movement | Network policies, access paths, testing results |
| Recovery | Restore tests completed for critical services with verified recovery time | Restore evidence, runbooks, RTO and RPO tracking |
This approach also reduces performative cybersecurity. A control is not a purchase. It is a capability you can demonstrate under pressure.
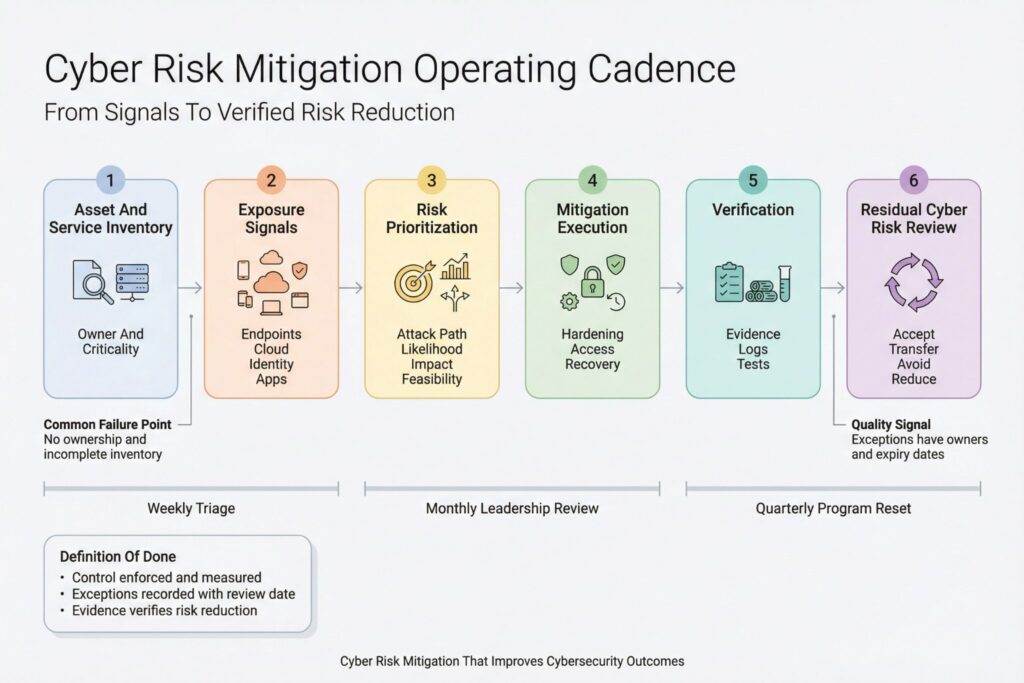
Run Cyber Mitigation as a Weekly Cadence
Cyber risk mitigation becomes reliable when it runs like an operating model rather than a project. A workable cadence turns signals into actions and actions into verified reduction.
Set a steady rhythm that people can plan around. Weekly triage works well for high-exposure findings and identity issues. Monthly leadership review works for exceptions, third-party risk, and investment decisions. The goal is predictable throughput and predictable escalation.
Programs commonly stall for reasons that have nothing to do with scanners. Ownership is unclear for shared services. Business criticality is undefined, so every system is treated as a crown jewel. Exceptions become permanent because no one schedules review. Engineering receives fix requests without impact context, so feature work always wins.
Treat exceptions like liabilities. If an exception is necessary, it has a compensating control when possible, an expiry date, and a named owner who accepts residual cyber risk on a schedule.
Third-party services require the same discipline. Mitigation includes contractual requirements for patching and incident notification, but it also includes technical boundaries such as segmented connectivity, minimal permissions for integrations, and continuous monitoring of key access paths.
Metrics That Prove Risk Went Down
Mitigation is measurable when metrics support decisions rather than decorate dashboards. Keep the set small, trend it over time, and attach each metric to an action when it turns red.
- Time to remediate high-exposure findings on internet-facing and high-impact systems
- Percentage of privileged access protected by strong authentication and monitored sessions
- Percentage of critical services with recent restore validation and tested recovery procedures
- Reduction in externally reachable attack surface such as open ports and admin endpoints
- Time to contain incidents that reach production systems
A final metric ties cyber mitigation to accountability. Track how much residual cyber risk is accepted, by whom, and for how long. Mature organizations accept some risk deliberately. Immature ones accept risk by default.
A 90-Day Plan You Can Execute
A mitigation program improves fastest when the first quarter is concrete. Aim for fewer initiatives, deeper completion, and tighter verification.
| Timeframe | Focus | Deliverables That Change Outcomes |
|---|---|---|
| Days 1 to 30 | Visibility and ownership | Service inventory with owners and criticality, top exposure paths identified, exception template in use |
| Days 31 to 60 | Identity and exposure | Privileged access under strong authentication, high-risk internet exposure reduced, remediation SLAs in place |
| Days 61 to 90 | Resilience and proof | Restore tests completed for critical services, segmentation priorities delivered, dashboard tied to decisions |
Cyber risk mitigation becomes credible when it is specific, owned, and verifiable. In 2025, the organizations that improve fastest are not the ones with the most controls. They are the ones that turn a short list of high-impact actions into repeatable habits and can show, with evidence, that risk actually went down.
Frequently Asked Questions (FAQ)
Start with attack paths that are both plausible and business damaging. Prioritize internet-facing access, privileged accounts, and systems that support revenue or regulated data. If you cannot explain the order to a non-security leader in two sentences, the prioritization model is too complex.
Done means the control is enforced, coverage is measured, exceptions are recorded with owners and review dates, and the result can be verified using evidence such as logs or configuration state. A control that exists only as a policy or a pilot is not done. A control that is deployed but not monitored is also not done.
Accept risk only when the cost or disruption of mitigation outweighs the likely impact, and when leadership explicitly owns that decision. Risk acceptance should name the system owner, define the scope, set an expiry date, and describe compensating controls. If acceptance has no review date, it will quietly become permanent.
Use metrics that change what teams do next. Track time to remediate high-exposure findings on critical systems, coverage of strong authentication for privileged access, and recent restore validation for critical services. If a metric does not trigger an action when it worsens, it becomes reporting noise.
Security should own the risk model, prioritization, and verification. System owners in engineering, IT operations, and product teams should own remediation work and timelines because they control deployment risk and outages. Procurement should own third-party obligations, while security validates that contractual and technical controls reduce risk in practice.

Leave a Reply