A Cyber Attack is a deliberate attempt to compromise systems or data by breaking confidentiality, integrity, or availability. This article explains the main vectors seen in modern cybersecurity incidents and gives operational steps that reduce real risk across cloud, hybrid, and on-prem environments.
Cyber Attack Entry Points
Attackers rarely need creativity. They need one dependable foothold, then they expand. In incident response data from Mandiant, exploitation was the most common initial infection vector in 2024 at 33%, and stolen credentials were second at 16%. Those two paths alone account for almost half of observed initial access and they map directly to what defenders control day to day.
Verizon’s 2024 DBIR shows how credential abuse concentrates in web-facing compromises. In the Basic Web Application Attacks pattern, stolen credentials appear in 77% of breaches, which is consistent with large-scale credential stuffing against SaaS, VPN, and customer portals during an attack.
Treat vectors as business entry points with owners, not just technical categories. A helpdesk password reset flow, a finance approval change, a contractor onboarding checklist, and a third-party integration token are all cyber risks. If no one owns them, they become the easiest path.
A practical way to prioritize is to list your top ten externally reachable surfaces and top ten workflows that can move money or grant access.
Then ask two questions. What would an attacker try first, and what would you notice first. If you cannot answer the second question with specific logs and alerts, the vector is effectively unmonitored.
Harden Identity And Access Paths
Identity is a primary battlefield because it scales across every system. Microsoft reports that password-based attacks make up over 99% of 600 million daily identity attacks observed in Microsoft Entra data, and that it blocked 7,000 password attacks per second over the past year. This is why cybersecurity programs that still treat identity as an IT hygiene task struggle to contain modern cyber activity.
Start with accounts that can change permissions, move funds, or access sensitive data, then expand. The goal is to make credential theft expensive and short-lived.
Operational controls that consistently reduce compromise:
- Require phishing-resistant MFA for administrators, email, remote access, and developer tooling, then extend it to all users where feasible. Mandiant explicitly recommends stronger MFA for privileged access because phishing remains a common path to initial access and persistence.
- Enforce conditional access that ties access to device trust and risk signals. High-risk sessions should be blocked or require step-up authentication rather than relying on a single login decision.
- Reduce standing privilege using just-in-time elevation, separate admin identities, and routine entitlement reviews. Most organizations have more high-privilege accounts than they think, especially in SaaS admin consoles and CI systems.
- Standardize session revocation. A password reset is not enough if refresh tokens remain valid. Your incident playbook should include token revocation and device sign-out for the affected identity, not just credential rotation.
What good looks like is measurable. Password-only access should be impossible for email and any admin surface. New MFA methods, new device registrations, and new delegated admin privileges should be rare enough that you can review them quickly after an attack.
Reduce Exploitation And Misconfig Risk
Exploitation remains common because exposed assets are hard to inventory and patching is constrained by uptime requirements, legacy dependencies, and scattered ownership. Mandiant’s data keeps exploitation at the top of initial access, which is a signal that exposure management and patch execution are still inconsistent across many environments.
The most effective change is to treat exposure management as a continuous capability rather than a quarterly scan and a spreadsheet.
Key practices that prevent repeatable failure modes
Maintain a live inventory of internet-facing assets, including subdomains, old VPN endpoints, API gateways, and forgotten admin consoles. Unknown assets are unpatched assets.
Patch by exploitability and exposure, not by score alone. For edge devices, patch windows should be defined in days, not months. When patching is delayed, compensate by reducing exposure. Close management ports, restrict access by allowlist, and add WAF or reverse proxy controls where possible.
In cloud environments, misconfiguration often matters as much as missing patches. Public storage exposure, overly broad IAM, and permissive cross-account roles turn minor mistakes into major cyber incidents when combined with stolen credentials. Make drift detection a routine operational check, not a periodic audit.
Constraints and boundaries matter. In OT or ICS environments, patch cadence can be slow and change windows can be limited. In those cases, prioritize segmentation, strict remote access controls, and monitoring at the network boundary. For small teams, the realistic target is not perfect patching, it is fast patching on exposed assets plus compensating controls everywhere else.
Cyber Attack Detection And Response
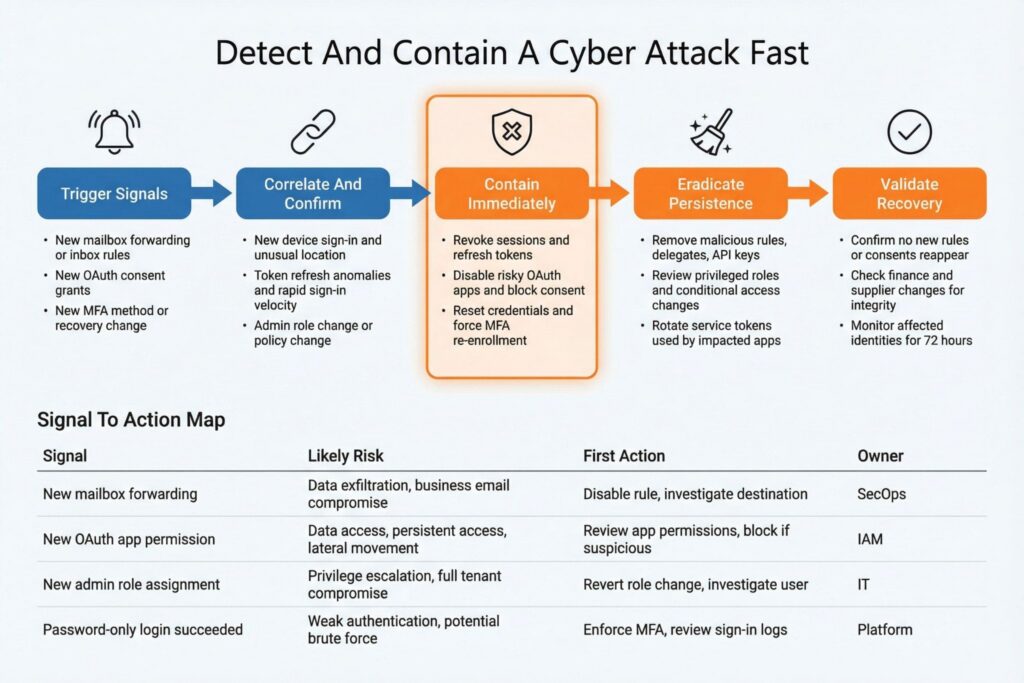
Early detection is rarely about spotting advanced malware first. It is about catching the actions that enable persistence and monetization. That is especially true for identity-led Cyber Attack chains where the attacker may never drop a traditional payload.
Mini-scenario: A finance manager receives a realistic vendor message and signs into a fake portal. The attacker uses the valid session to create a mailbox forwarding rule and adds an OAuth app with broad mail permissions. The SOC correlates two signals, a new inbox rule and a risky consent grant, then revokes sessions and blocks the OAuth app tenant-wide. IT forces a credential reset, resets MFA using phishing-resistant keys, and reviews admin consent settings. Finance confirms no payment details changed, and the team adds an out-of-band verification step for bank detail updates for high-risk suppliers.
This scenario is common because it uses the cheapest tools available. The defender advantage is that the key actions generate specific logs if you turn them on and route them centrally.
High-signal data to collect and alert on includes:
- Mailbox forwarding and inbox rule creation, especially for finance and executive roles
- OAuth consent grants and new enterprise application permissions
- New MFA method enrollment and changes to recovery information
- Privileged role assignments and changes to conditional access policies
- Unusual token refresh patterns and sign-ins from new devices for sensitive applications
Make ownership explicit. Security detects and coordinates, IAM owns access policy, platform teams own patch execution, and application teams own service tokens and integration scopes. A cyber incident fails when a signal is detected but no one has clear authority to act.
Prepare For Disruption And Extortion
Availability attacks and extortion are not separate from vectors. They often follow the same initial access paths and then pressure the business through downtime. Planning for disruption is a cybersecurity control because it reduces the attacker’s leverage.
Define restoration priorities for critical services and dependencies, then test restoration under time pressure. Backups that have never been restored in a realistic exercise are assumptions, not resilience.
Keep offline or immutable backups for crown-jewel systems, especially directory services, identity providers, and key data stores. Extortion becomes harder when recovery is predictable.
Validate that admin paths for backup systems are isolated from standard user credentials. If the same identity that reads email can administer backups, a single phish can become a full-environment outage.
Cost data explains why disruption planning matters. IBM reported a global average breach cost of USD 4.88 million in 2024, with a 10% increase year over year, and noted that business disruption and post-breach response activities drive much of the cost. Even when data loss is limited, operational interruption often becomes the largest business impact.
Prove Controls With Measurements
Metrics should validate outcomes, not activity. Choose measures that map to the vectors you face and that trigger a concrete operational response when they fall short.
| Vector focus | Control that matters most | Validation check that proves it |
|---|---|---|
| Credential theft | Phishing-resistant MFA and conditional access | Privileged users on phishing-resistant MFA and password-only logins blocked |
| Web exploitation | Asset inventory and patch prioritization | Time to patch exploited-in-the-wild issues on internet-facing assets and unknown exposed services found monthly |
| Email and SaaS abuse | Mailbox and OAuth monitoring | Time to detect and reverse forwarding rules or risky consent grants |
| Cloud misconfiguration | Least privilege and drift detection | Weekly checks for public storage exposure and high-risk IAM policy changes |
| Disruption readiness | Restore testing and admin isolation | Recovery time results for critical services and successful restore rate in drills |
Keep targets small and enforceable. For many organizations, the highest-value targets are full phishing-resistant coverage for privileged access, complete ownership for public-facing assets, and a defined maximum patch window for critical exposed systems. Hitting those targets does not eliminate every cyber attack, but it sharply reduces the number that turn into material incidents and it makes containment faster when one slips through.
Frequently Asked Questions (FAQ)
A cyberattack vector is the entry path into your environment, such as stolen credentials, an exposed service, or a misconfigured cloud resource. An attack technique is what happens after entry, such as privilege escalation, lateral movement, or persistence.
Start with identity.
Look for new mailbox forwarding rules, newly created inbox rules, and suspicious OAuth consent grants. Pair those with unusual sign-ins from new devices or atypical locations for the same user.
If an account can change permissions, approve payments, access sensitive data, or administer backups, phishing-resistant MFA should be mandatory. That includes admins, finance, executive assistants, and anyone with access to customer data systems.
Revoke active sessions and refresh tokens, not just the password. Also review and remove newly added MFA methods, mailbox rules, and any new OAuth apps tied to the account.
Backups should be restorable within defined time targets, and the restore process should be tested under realistic constraints. Backup administration should be isolated from standard user credentials to prevent a single phish from turning into full-environment loss.

Leave a Reply