-
Posted by
on
What is Security Analytics?
Security analytics is how a security team turns raw cybersecurity telemetry into decisions it can explain, repeat, and improve. Done well, it reduces time wasted on noise and increases the share of…
-
Posted by
on
What Is a Security Misconfiguration
Security misconfiguration is a security weakness caused by unsafe settings in systems that otherwise work as designed. Nothing is broken in the usual sense. The problem is that a control exists but…
-
Posted by
on
Cyber Risk Mitigation Strategy
Cyber risk mitigation is the set of decisions and actions that reduce the likelihood of a cyber incident, reduce the impact when an incident occurs, or improve recovery so the business can…
-
Posted by
on
What Is a Risk Heat Map for Cyber Risk
A risk heat map is useful only when it changes what people do next. In cybersecurity, teams can drown in scanner findings, cloud misconfigurations, identity alerts, and third party issues while the…
-
Posted by
on
Addressing IoT Security Challenges in Real-World Environments
IoT cybersecurity fails most often for a simple reason. Devices arrive faster than organizations can inventory, segment, and govern them. IoT Analytics estimated 18.5 billion connected IoT devices in 2024 and projected…
-
Posted by
on
What Is the NIST Cybersecurity Framework CSF 2.0
Cybersecurity risk is now a core business risk with measurable financial impact. IBM’s 2024 Cost of a Data Breach Report put the global average cost of a breach at USD 4.88 million,…
-
Posted by
on
Cybersecurity Automation: The Survival Mechanism for Modern SOCs
The speed of cyber defense has historically lagged behind the speed of attack. In 2024, the IBM Cost of a Data Breach Report highlighted a stark reality. Organizations that extensively deployed artificial…
-
Posted by
on
Why Security Posture Is About Resilience, Not Just Compliance
Global spending on cybersecurity and risk management technology continues to rise annually, yet the frequency and severity of data breaches show no sign of slowing down. This disconnect highlights a fundamental misunderstanding…
-
Posted by
on
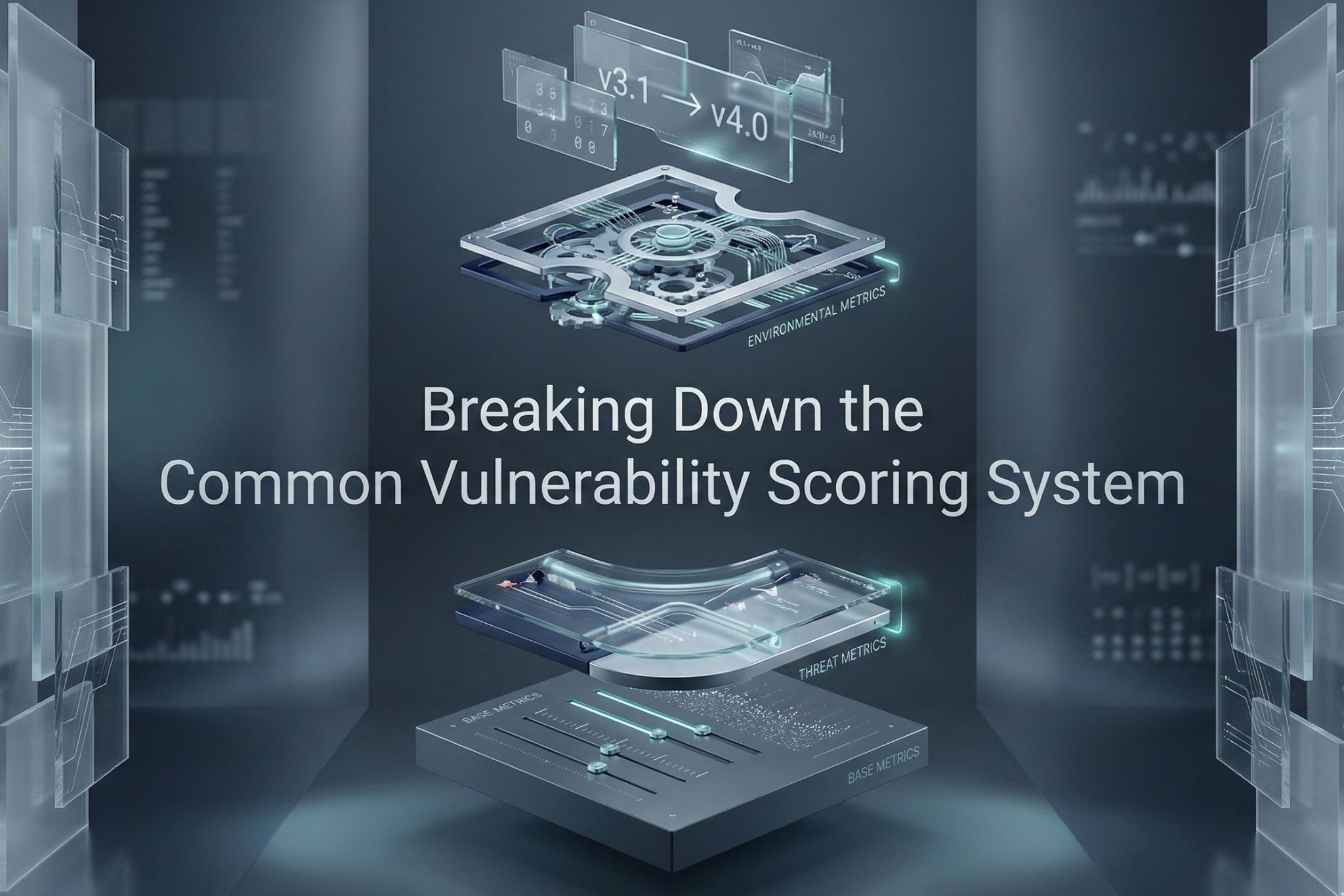
Breaking Down the Common Vulnerability Scoring System
Security teams frequently equate severity with risk, a miscalculation that leads to inefficient patch management and resource exhaustion. The Common Vulnerability Scoring System (CVSS) offers a standardized framework for assessing the technical…
-
Posted by
on
Vulnerability Management vs. Vulnerability Scanning
Security professionals in 2026 grapple with a math problem that no human team can solve manually. The National Vulnerability Database recorded over 29,000 new entries in 2024 alone, and the trajectory for…