Modern organizations rely on third parties for core workflows, infrastructure, and customer-facing capabilities. Vendor risk management in cybersecurity is the operating system that decides which third-party relationships are acceptable, what security and resilience requirements apply, and how those requirements are verified over time. A workable program reduces real exposure without turning onboarding into a slow, paperwork-driven process.
Define Vendor Risk Program Boundaries
Vendor risk management breaks down when vendor is defined too narrowly or when ownership is unclear. Set boundaries around third parties that store, process, transmit, or can access your data or systems, or could materially disrupt critical operations if they fail. Include SaaS platforms, managed service providers, payment-related partners, cloud agents, contractors with privileged access, and outsourced development or support functions.
Anchor the program in governance so decisions are repeatable and defensible. Governance-oriented frameworks emphasize accountability and oversight, which is directly applicable to third-party risk decisions (NIST, Cybersecurity Framework 2.0, 2024).
Translate that into an internal ownership model that works in daily operations:
- Security defines the minimum control baseline by tier, the evidence you will accept, and escalation thresholds.
- Procurement and Legal negotiate terms, enforce leverage, and maintain contractual records.
- The business owner of the relationship accepts residual risk and ensures the vendor is used only within approved scope.
- IT and Engineering validate technical claims and implement integrations in a controlled way.
If your organization lacks centralized intake, create a simple gate: no vendor receives production credentials or production data until it is inventoried, tiered, and approved with a named owner. This is less about bureaucracy and more about preventing “silent” exposure that cannot be tracked later.
Tier Vendors By Impact
A practical way to improve coverage is to avoid treating all vendors equally. Tiering should reflect impact, not vendor brand or spend. A consistent tier model reduces debate and helps teams understand why certain evidence or contract language is required.
Use three impact dimensions and apply them to each vendor’s intended use:
- Data sensitivity and volume the vendor touches.
- Privileged access or connectivity into your environment.
- Business criticality and recovery dependency.
A compact tiering model can look like this:
| Vendor Tier | Typical Exposure | Minimum Due Diligence |
|---|---|---|
| Tier 1 Critical | Regulated data, identity integrations, production admin access, high availability dependency | Independent assurance evidence, architecture review, resilience validation, enforceable contract controls |
| Tier 2 Significant | Customer or internal confidential data, limited production access, important business process | Targeted questionnaire, evidence for key controls, security addendum, onboarding review |
| Tier 3 Limited | No sensitive data, minimal access, low operational dependency | Basic screening, standard terms, least-privilege provisioning |
This approach aligns with risk-based supply chain guidance that emphasizes selecting controls based on exposure and maintaining them over time, rather than relying on one-time checklists (NIST, SP 800-161 Rev. 1, 2022).
Request Evidence For Key Controls
Assessments should answer a single operational question: can the vendor protect what you will expose and recover quickly enough when something fails. Prefer short, verifiable requests over long questionnaires that generate unverifiable claims. Tie evidence to the integration model, the data flows, and the failure modes that matter to your environment.
Prioritize evidence in areas that are both high-impact and commonly weak:
- Identity and access management for your integration, including MFA, least privilege, and admin segregation.
- Change management and secure development practices if the vendor ships code that affects you.
- Vulnerability and patching practices, including how urgent issues are triaged and communicated.
- Logging and monitoring relevant to the service you will use, including what you can access.
- Incident response readiness, including notification mechanics and cooperation expectations.
- Business continuity and disaster recovery, including proof of tested restoration for the region or deployment model you use.
When the vendor provides independent assurance (for example, third-party audit reports), treat it as a starting point, not a substitute for environment-specific questions. Close the gap between a generic control statement and your actual usage: the same service may be low risk in one integration and high risk in another.
Practical Mini Scenario
An engineering team proposes a SaaS support tool that needs OAuth access to customer tickets and can retrieve attachments. You tier it as Tier 2 because it touches customer data but does not require production admin access. The vendor provides independent assurance evidence, but cannot demonstrate tested restore procedures for the specific region you will use and offers vague incident notification language. You proceed only after adding a contract requirement for a defined notification window and limiting the integration to read-only access with attachment scanning, then schedule quarterly access reviews with a named owner.
Embed Controls In Contracts
Evidence without enforceable obligations is fragile. Contracts convert expectations into terms that survive staffing changes, vendor reorganizations, and business pressure. Focus on terms that matter during real incidents and audits, and keep them tiered so Legal can apply consistent language.
Use contract controls that map to the vendor’s tier and your specific service scope:
- Clear security obligations tied to the agreed access model and data types.
- Incident and breach notification requirements, including timing, content, and contact paths.
- Subcontractor and subprocessor governance, including flow-down expectations and change notification.
- Cooperation for investigations, including log retention, preservation, and reasonable support.
- Audit rights or an agreed cadence for receiving independent assurance evidence.
- Data handling boundaries, including location constraints where applicable, deletion, and return on exit.
- Resilience expectations for critical services, including recovery objectives and evidence of testing.
For Tier 1 vendors, add operational hooks that allow rapid action: escalation paths, emergency access suspension procedures, and clear points of contact. Keep these clauses realistic: define what you expect, how quickly, and what happens if the vendor cannot meet the requirement.
Run Ongoing Vendor Monitoring
Third-party risk changes after onboarding. Vendors change hosting, add subprocessors, alter product features, and experience incidents. Monitoring should not mean buying more alerts than you can handle. It means selecting a small set of signals that have clear owners and clear actions.
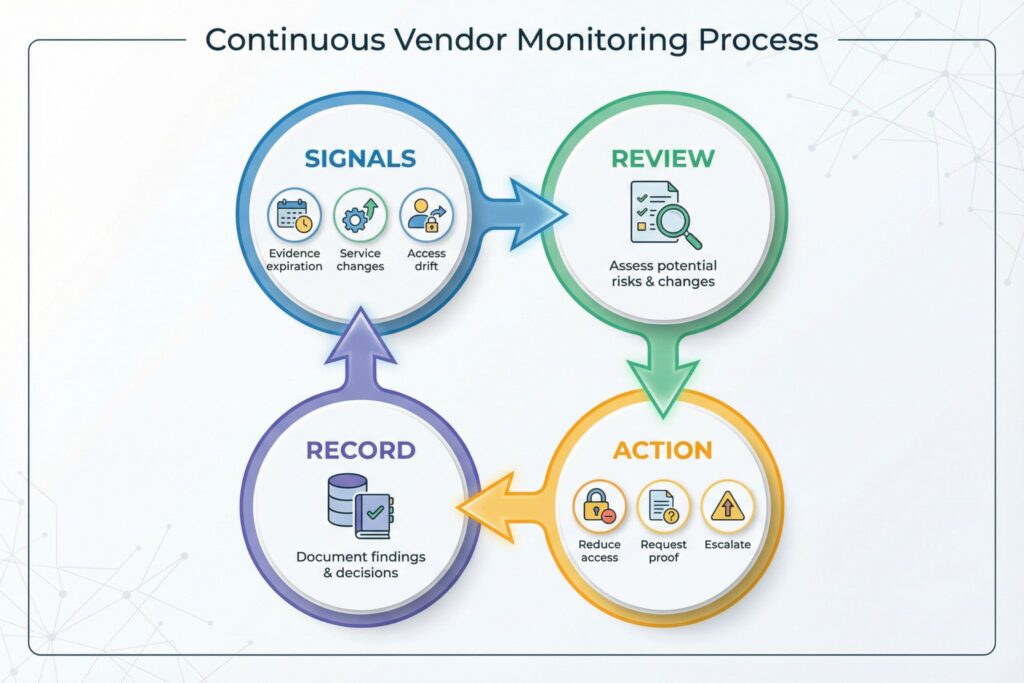
Operational signals that are usually actionable:
- Assurance evidence expiration dates and overdue renewals by tier.
- Material service changes that affect data flows, access scopes, or hosting model.
- Security advisories relevant to your integration, agents, or deployed components.
- Access drift in your environment, such as new API keys, expanded scopes, or new admin roles.
- Vendor incident notifications, including severity classification and required follow-up steps.
Treat offboarding as part of monitoring, not a separate project. Ensure you can revoke access quickly, rotate shared secrets, disable integrations, and validate data deletion or return. For Tier 1 vendors, run at least one coordination drill or documented walk-through that tests contact paths, decision rights, and the sequence for isolating the vendor relationship during an incident.
Measure Outcomes And Exceptions
A program that cannot show outcomes will either over-restrict the business or quietly decay. Track a small set of metrics that reflect reduced exposure and faster response, and review them with Security, Procurement, and business owners on a consistent cadence.
Use metrics that are easy to compute and hard to game: coverage of Tier 1 and Tier 2 vendors with current assurance evidence and signed security addenda; time to complete onboarding by tier with root causes for rework; count of vendors with privileged access and the share reviewed within the last quarter; time to revoke vendor access after termination or role change; and vendor-related security incidents with time from vendor notification to internal containment actions.
When exceptions occur, require compensating controls, assign an expiration date, and record who accepted the residual risk. This keeps exceptions visible and prevents temporary risk from becoming permanent.
Frequently Asked Questions (FAQ)
Reduce exposure first by limiting data shared, constraining permissions, and isolating integrations. If the vendor remains high impact, treat refusal as a risk signal and require explicit executive risk acceptance with compensating controls and a renewal gate tied to evidence delivery.
Independent evidence is useful, but it rarely answers environment-specific questions such as integration scope, recovery for your deployment region, and incident cooperation details. Use it as input, then request targeted proof for the controls that map to your access model.
Use a tiered cadence and change triggers. As an operational baseline, many teams reassess Tier 1 annually, Tier 2 every 18–24 months, and Tier 3 through lightweight screening, with immediate review after material changes such as new data types or new privileged access.
Inventory vendors with access and remove unnecessary access. Privileged access reduction, credential rotation, and strict scope management usually reduce exposure faster than expanding questionnaires.
Limit monitoring to signals you will act on and route each signal to a named owner. Track assurance expiration, access drift, and major service changes, then enforce quarterly reviews for the highest-impact vendors.

Leave a Reply