Common Vulnerabilities and Exposures, usually shortened to CVE, is the global naming and cataloging system used to track publicly disclosed security vulnerabilities. A CVE entry gives the security community a consistent way to reference the same weakness across vendor advisories, scanning tools, ticketing systems, and patch notes. Without that shared identifier, teams often waste time reconciling duplicate names or ambiguous descriptions.
CVE is best understood as a coordination layer. It does not patch anything by itself, and it is not a severity rating. Its value is precision: one vulnerability, one identifier, many systems speaking the same language.
What CVE Represents in Real Security Work
A CVE typically appears when a vulnerability is disclosed and needs an identifier that can be referenced reliably. The identifier looks like CVE-YYYY-NNNNN, where the year helps orient disclosure timing and the numeric part distinguishes the record from others.
In practice, CVE enables you to:
- Track a vulnerability from discovery to remediation across teams and tools
- Match vendor fixes and mitigations to the correct issue
- Correlate scanner findings, threat reports, and incident evidence to one record
- Produce audit-ready reporting that points to a stable, public reference
What Counts as a Vulnerability in CVE
CVE focuses on publicly disclosed vulnerabilities: weaknesses in software, firmware, or hardware that can be exploited to impact confidentiality, integrity, or availability. The key word is exploitable. A functional bug that cannot be abused for security impact is often handled outside CVE, depending on the reporting organization and program rules.
This boundary matters for readers because it explains why some risky situations do not have CVE IDs. For example, insecure default configurations, risky deployments, or weak operational processes can create real exposure without mapping cleanly to a single product vulnerability record.
CVE ID vs CVE Record
People often say a product has a CVE, but there are two distinct elements:
- CVE ID: the unique identifier assigned to the vulnerability
- CVE Record: the structured description published for that ID, including references and metadata, and sometimes affected version details
This distinction helps set expectations. Early in disclosure, the CVE Record may contain minimal information, then gain clarity as maintainers publish advisories, researchers add technical analysis, and affected-version data is refined.
Who Assigns CVEs and Why It Matters
CVE IDs are assigned by authorized organizations called CVE Numbering Authorities, or CNAs. CNAs include vendors, open-source projects, security research groups, CERT organizations, bug bounty providers, and others with defined scope. Their job is to assign CVE IDs for vulnerabilities within that scope and publish the corresponding CVE Records.
In April 2025, CISA executed an 11-month option period on the contract that funds MITRE’s operation of the CVE Program, avoiding a lapse in CVE services and extending the contract period into March 2026.
Why this matters operationally: the quality and completeness of a CVE Record depends on what the CNA knows at publication time. A well-maintained project might provide precise affected versions and mitigation guidance quickly, while other records may remain sparse until more details emerge.
CVE Statuses You Will See
CVE records can change status as information evolves. Two statuses are especially important for day-to-day work:
- Published: the CNA has populated and released the CVE Record
- Rejected: the ID and record should no longer be used, typically due to duplication or because the issue was determined invalid as a vulnerability
Security teams should treat Rejected CVEs as an explicit signal to close or re-map internal tickets, rather than silently ignoring them.
How CVE Relates to NVD
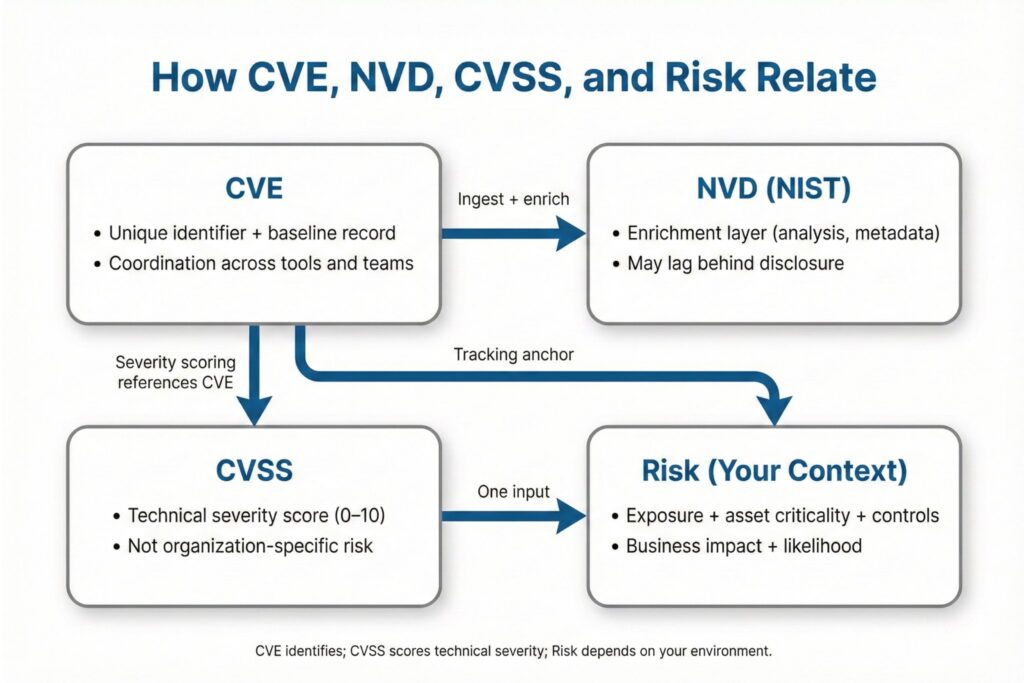
CVE and the National Vulnerability Database are connected but not interchangeable. CVE provides the identifier and baseline record. NVD, operated by NIST, ingests CVE records and adds enrichment such as analysis and additional data fields used by many tools and dashboards.
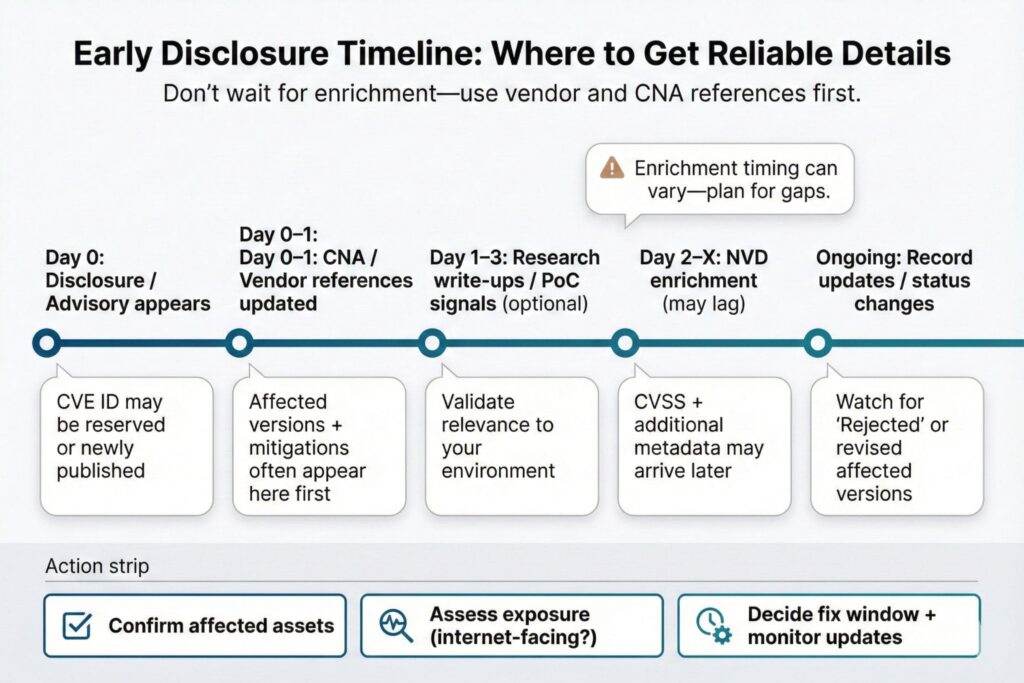
A practical caution: NVD enrichment can lag behind disclosures. Since February 12, 2024, NVD enrichment has experienced a major slowdown and a growing backlog; NIST has stated it is prioritizing analysis of the most significant vulnerabilities while bringing on additional support, and it deployed a redesigned NVD vulnerability search experience in July 2025.
If your processes depend on NVD timing, plan for gaps by using vendor advisories and CNA references as primary sources during the first days of a disclosure.
CVE Is Not CVSS and Not Risk
CVE identifies the vulnerability. CVSS scores its technical severity under a standardized model. CVSS is designed to be broadly consistent and organization-agnostic, but it cannot fully capture your environment, asset criticality, compensating controls, or exposure.
This is why two organizations can see the same CVE and make different decisions. A high CVSS score on an internal system behind multiple layers of access control may be lower priority than a medium score on an internet-facing service that is core to revenue.
How to Use CVEs for Better Prioritization
A disciplined workflow uses CVE as the tracking anchor and layers context on top. In most organizations, the fastest path to value looks like this:
- Confirm you actually run the affected product and versions
- Determine exposure: internet-facing, internal-only, or isolated
- Check whether a fix exists and how disruptive it is to deploy
- Look for evidence of exploitation or active interest from attackers
- Document decisions and re-check as records and advisories update
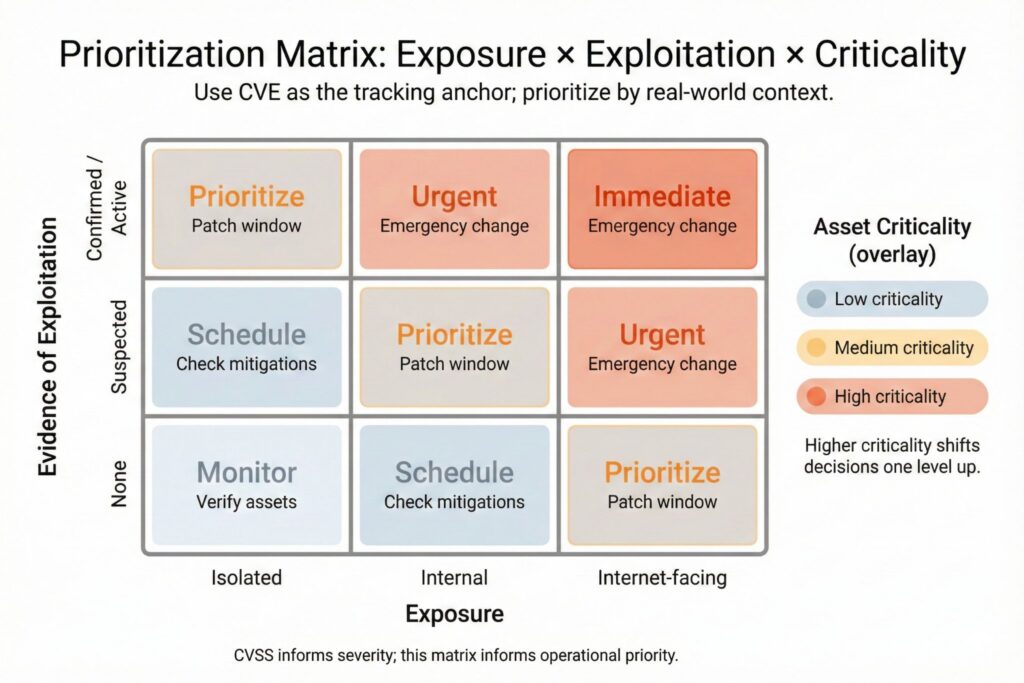
This approach reduces noisy fire drills driven by headlines while still catching urgent, real-world threats.
Common Misunderstandings That Cause Missed Work
CVE systems are widely used, which also means they are widely misused. The most common pitfalls are:
- Assuming no CVE means no problem, even when exposure is clearly present
- Treating CVSS as a complete risk decision instead of one input
- Waiting for NVD enrichment when vendor guidance is already available
- Ignoring Rejected status and keeping stale tickets open
Common Vulnerabilities and Exposures in CVE is the shared reference system that makes vulnerability management scalable. It provides a stable identifier and record so the industry can coordinate disclosure, tooling, and remediation. Use CVE to track and correlate, use scoring systems like CVSS to inform severity, and use your environment context to decide what to fix first.
Frequently Asked Questions(FAQ)
Is CVE a database or a standard?
CVE is a standardized identification system for publicly disclosed vulnerabilities, supported by a program that publishes CVE Records used across many databases and tools.
Does every vulnerability get a CVE?
No, some issues are never assigned a CVE due to scope rules, incomplete disclosure, or because the issue is handled as a configuration or operational risk rather than a product vulnerability.
What is the difference between CVE and CVSS?
CVE identifies the vulnerability, while CVSS provides a severity score that helps compare technical impact under a consistent model.
Why might a CVE record have limited details at first?
Early disclosure often happens before full analysis is complete, so records may be updated as vendors and researchers confirm affected versions and add references.
What should I do if a CVE is marked Rejected?
Stop using that CVE ID for tracking and look for the corrected or duplicate identifier referenced by the rejection notice, then update internal tickets accordingly.
Leave a Reply