Tactics, techniques, and procedures, usually shortened to TTPs, describe how an adversary behaves while attempting to compromise a system. They matter because attackers can swap out malware, infrastructure, and domains quickly, while their underlying behaviors often stay recognizable.
Understanding Tactics Techniques Procedures
NIST defines TTPs as the behavior of an actor, with tactics as the highest-level description, techniques as more detailed behavior in the context of a tactic, and procedures as the lowest-level, highly detailed description in the context of a technique in cyber incidents.
For defenders, the easiest mental model is intent, method, and execution.
A tactic explains the adversary’s objective at a point in time. Examples include initial access, privilege escalation, and exfiltration. It is the why.
A technique is the approach used to achieve that objective. Phishing, exploitation of a public-facing application, and credential dumping are techniques. It is the how.
A procedure is what the technique looked like in a specific incident, in your environment. It includes the concrete steps, tools, commands, and sequence that actually occurred. It is the how exactly, including the implementation details that matter for scoping and containment in cybersecurity operations.
Distinguishing TTPs From Indicators
TTPs are often confused with indicators of compromise. Indicators are artifacts such as IP addresses, domains, file hashes, file names, registry keys, or email sender infrastructure. They are useful for fast blocking and enrichment, but they tend to expire quickly when an actor rotates infrastructure.
TTPs are more durable because they describe behavior. If you build detection and response around techniques and their observable effects, you are less dependent on fragile artifacts. In practice, most mature programs use both. Indicators accelerate triage and containment. TTPs help you prevent a repeat in cyber defense.
A practical way to separate them is to ask what will still be true if the attacker changes tooling tomorrow. A hash likely will not. A pattern such as suspicious remote service creation, unusual identity provider configuration changes, or abnormal lateral authentication patterns might.
Mapping TTPs Across The Enterprise
MITRE ATT&CK is a widely used knowledge base that organizes adversary tactics and techniques based on real-world observations and provides a shared vocabulary across teams and vendors in cybersecurity.
Mapping to ATT&CK is valuable when it drives decisions, not when it turns into a labeling exercise. CISA’s mapping guidance highlights common mapping mistakes and analytical biases, and it explicitly notes that not every adversary behavior is documented in ATT&CK.
Use mapping to answer operational questions such as these.
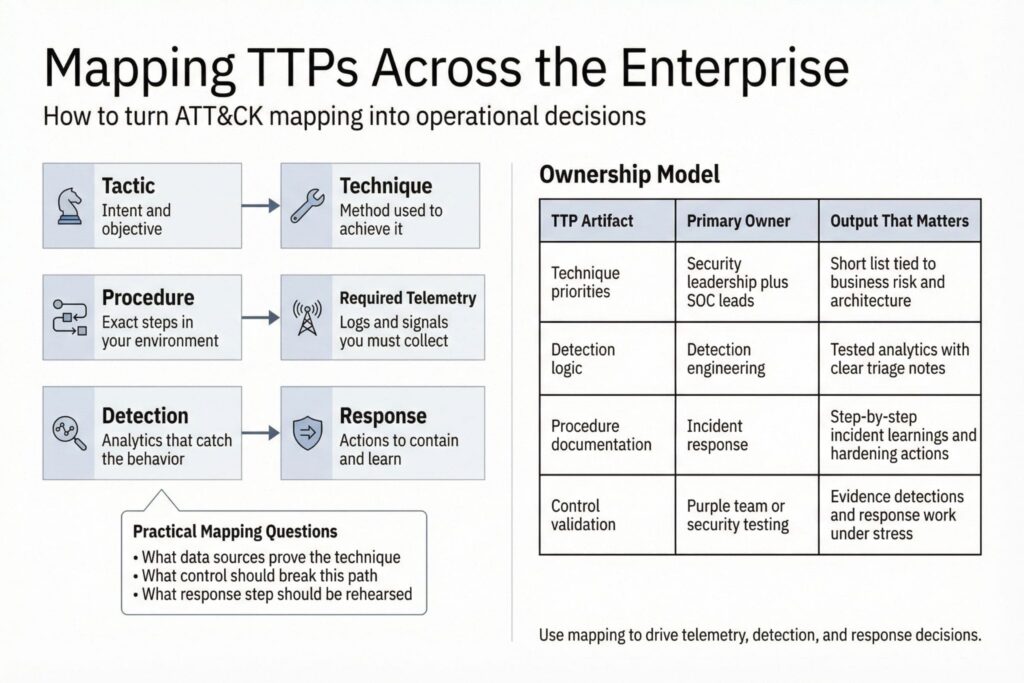
- Which data sources are required to observe a technique with confidence.
- Which controls should break the kill chain for that technique in your environment.
- Which detection rule needs tuning, and which response step should be rehearsed.
A compact ownership model helps keep mapping actionable.
| TTP artifact | Primary owner | Output that matters |
|---|---|---|
| Technique priorities | Security leadership plus SOC leads | A short list tied to business risk and architecture |
| Detection logic | Detection engineering | Tested analytics with clear triage notes |
| Procedure documentation | Incident response | Step-by-step incident learnings and hardening actions |
| Control validation | Purple team or security testing | Evidence that detections and response work under stress |
Building Detections Around Techniques
Start with a limited set of techniques that fit your environment and that you can observe reliably. A small team does better with ten well-instrumented techniques than with a spreadsheet of a hundred unmapped aspirations.
Good technique-driven detection work starts with telemetry. For many enterprises, the minimum set includes endpoint process and command-line telemetry, authentication logs, network DNS and proxy data, and cloud control plane auditing where applicable. In SaaS-heavy environments, identity and cloud audit events often matter more than endpoint artifacts.
When you turn a technique into a detection, define what good looks like.
- Clear prerequisites, such as required log sources and fields.
- A primary behavioral condition, such as impossible travel paired with privileged access, or a new service created by a non-admin context.
- A small set of suppressions grounded in your environment, such as known automation accounts and maintenance windows.
- A triage path that tells an analyst what to check first and what data confirms or refutes malicious intent.
One common pitfall is building detections that are too literal. Procedures vary. Your detection should focus on the stable behavior and tolerate tool swaps, then use procedure-level details as enrichment in cybersecurity monitoring.
Using TTPs During Incident Response
TTPs are most valuable when an investigation is moving quickly and decisions are expensive. They help you predict what the attacker is likely to do next and where to look for evidence.
Mini-scenario: A SOC sees a burst of failed sign-ins followed by a successful login to a finance administrator account from a new network. The analyst correlates this with an unusual sequence of identity events and rapid creation of new persistence mechanisms, which points to an account compromise technique pattern rather than a simple password issue. The incident commander decides to contain immediately, revokes sessions, disables risky tokens, and blocks the source, while the responder scopes for related privileged actions across the tenant. The outcome is that the attacker loses access before high-value mailboxes and cloud storage are accessed, and the team adds a new response step that prioritizes identity persistence checks after any privileged sign-in anomaly.
CISA advisories often describe observed TTPs in enough detail to support this style of planning and hunting, including evolving social engineering approaches in active threat activity.
Constraints still apply. In multi-tenant cloud and SaaS, containment may hinge on identity controls, session revocation, and audit log integrity rather than reimaging endpoints. In OT and ICS environments, response actions may be constrained by safety and uptime requirements, and visibility may be network-centric, which is one reason CISA includes ICS-specific mapping guidance.
Measuring TTP Coverage With Evidence
Counting mapped techniques is not a meaningful maturity metric on its own. What matters is whether your program can observe, detect, and respond to the techniques you care about.
Use evidence-based measurements that connect to outcomes.
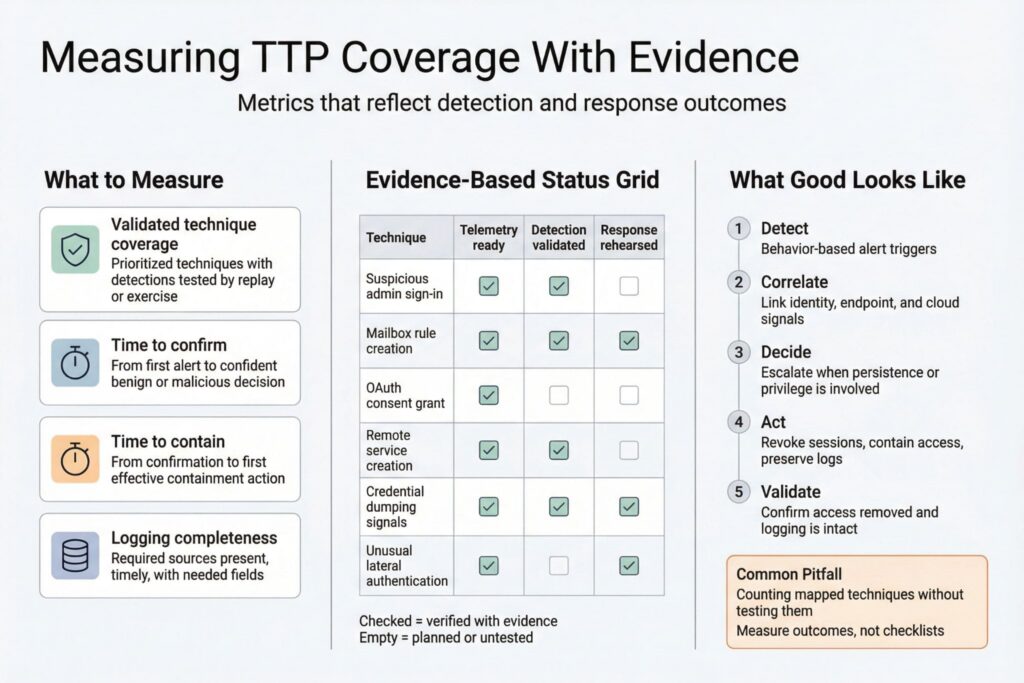
- Validated technique coverage, meaning prioritized techniques with detections tested through a controlled exercise or replayed incident data.
- Time to confirm, measured from first alert to a confident determination of benign or malicious behavior.
- Time to contain, measured from confirmation to the first effective containment action.
- Logging completeness, measured by whether required sources are present, timely, and include the fields your analytics depend on.
Revisit the prioritized techniques set regularly. ATT&CK evolves and your architecture changes, so technique selection should follow real exposure and incident learnings, not a static checklist in cybersecurity programs.
Frequently Asked Questions (FAQ)
No. Indicators are artifacts like hashes, domains, and IPs that can change quickly, while TTPs describe attacker behavior that often persists across campaigns and tooling swaps.
ATT&CK is a structured way to name and organize tactics and techniques so teams can map threats, detections, and incident learnings consistently. It is best used as a shared vocabulary that drives decisions about telemetry, analytics, and response playbooks.
A procedure is the concrete sequence of steps an attacker used in your environment, including specific commands, tools, identity actions, and timing. It is what responders document so the same path can be detected and blocked faster next time.
Ownership is shared. Threat intel prioritizes relevant behaviors, detection engineering builds and validates technique-based analytics, and incident response captures procedures and turns them into hardening actions.
It fires on stable behavior, not fragile artifacts, and it includes clear prerequisites and a triage path. It also stays useful after routine attacker changes like new infrastructure or a different malware family.

Leave a Reply